 Support for Drupal 7 is ending on 5 January 2025—it’s time to migrate to Drupal 10! Learn about the many benefits of Drupal 10 and find migration tools in our resource center.
Support for Drupal 7 is ending on 5 January 2025—it’s time to migrate to Drupal 10! Learn about the many benefits of Drupal 10 and find migration tools in our resource center.This issue adds information about contrib security advisory coverage to update status. #2804155: If the next minor version of core has a security release, status still says "Security update required!" even if the site is on an equivalent, secure release already improves version number handling for core.
Problem/Motivation
To support the recent changes to the project application process, namely decoupling the ability to create full projects/releases from security coverage - we need to provide indicators on the update status page of which installed modules receive security coverage.
@hestenet, @drumm, and @mlhess hope to help drive this forward. @Dries has given his blessing to prioritize this patch.
We (the DA) want to get this committed as soon as possible, and so we're allocating our sprint time towards getting this ready, writing tests, and responding to any reviews.
What is the problem to solve?
Drupal projects that do not have a stable release and haven’t opted into security advisory coverage have security issues reported to their public issue queues. This leaves lots of opportunity for attackers to learn about vulnerabilities and exploit them.
There are cases where you can be relatively safe running a non-covered project, but the average site owner will not be safe in general. Site owners should be informed of the risks.
Who is this for?
Primarily site owners. They should be informed of what security risks exist so they can plan and act accordingly.
Secondarily project maintainers. They should be encouraged to opt their projects into coverage and make stable releases.
Result: what will be the outcome?
A higher proportion of Drupal sites are running a higher proportion of covered releases.
How can we know the desired result is achieved?
Update status data reported to updates.drupal.org.
Proposed resolution
The changes would need to:
- Indicate which modules have security coverage and which do not.
- Provide visual indicators of coverage status via the shield icon and the !-alert icon
- For modules that are explicitly unsupported for known security issues or other reasons, it should indicate that
In addition the changes could:
- Provide an alert on each page for admins like the 'you are using a module with a security release' warning
Key Question:
"How do we keep users informed about which of their modules receive security advisory coverage, in a way that educates them rather than scaring them?"
Implementation questions to be resolved:
- Where should the list of covered/uncovered modules be presented?:
[ ] a. Only on the status page
[ ] b. Only on the updates page
[ ] c. Both
[X] d. Notify on the status page, but direct users to the updates page for per-module info. - If we put indicators on the updates page, what kind of indicators should we use?
[ ] a. Negative indicators on each module
[ ] b. Positive indicators on each module
[X] c. Both
[ ] d. A single warning at the top of the page, referring users to the list of uncovered modules on the status page.
[X] e. But separate the different indicators into separate columns - How loud should the "Your site uses modules that do not receive security advisory coverage from the security team" message be?
[ ] a. It should follow admins everywhere, like the 'security update available message'
[ ] b. It should be at the top of the updates page, and link to the status page
[X] c. We don't need an extra message at the top. - Should developers be able to suppress this warning, through settings.php? And if so, what should they be able to suppress?
[ ] a. The top message that follows admins around
[ ] b. The top message on the updates page
[ ] c. The warning/list of modules on the updates
[ ] d. The warning on the status page
[X] f. none of the above - We've chosen in question 3 *not* to have any message follow you around, except for the normal 'there are warnings on your status page'
[ ] g. all of the above - Should we modify the way the colors work?
[X] a. Separate the updates rows into columns for: module name, version, up-to-date status, coverage status
[?] b. Eliminate the background colors entirely in favor of iconography
[X] c. Eliminate the background colors except for the RED warning on security updates
Remaining tasks
Before we roll this into core we may want to email maintainers to let folks know that this change is coming.
User interface changes
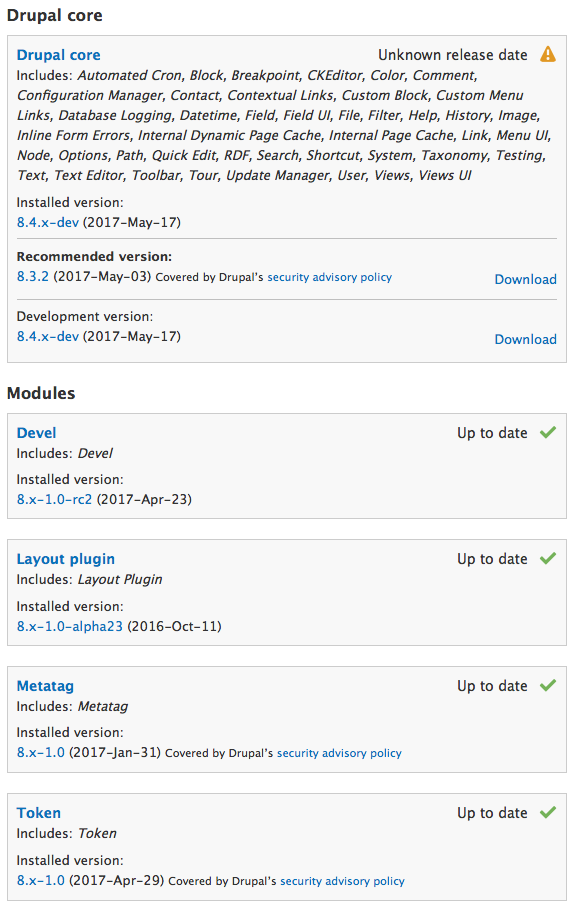
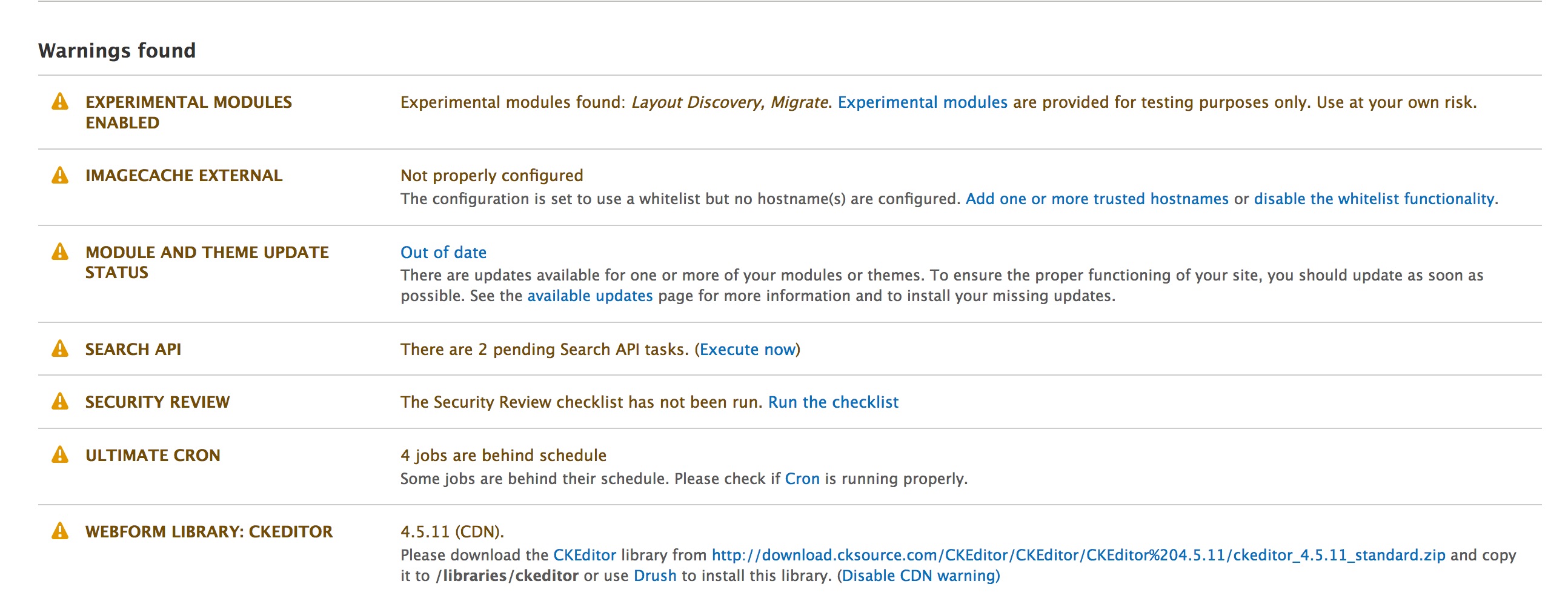
admin/reports/updates with added security information
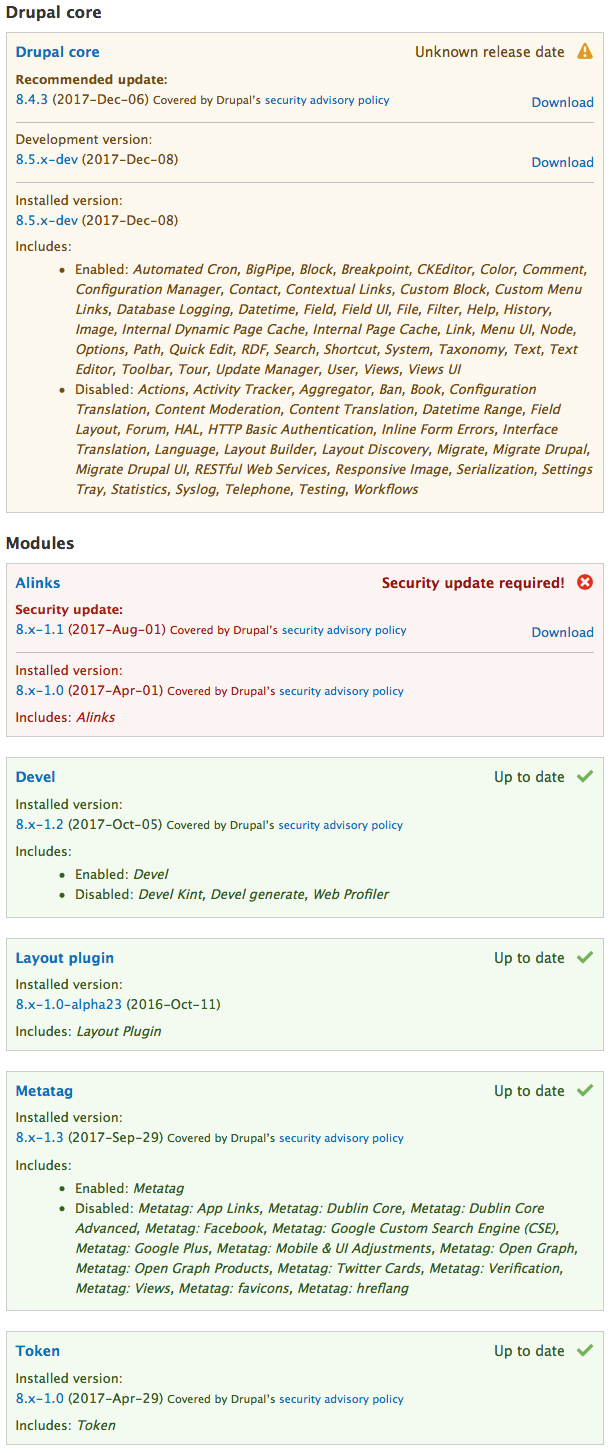
The update status for available updates, such as security updates, is left as-is for consistency.
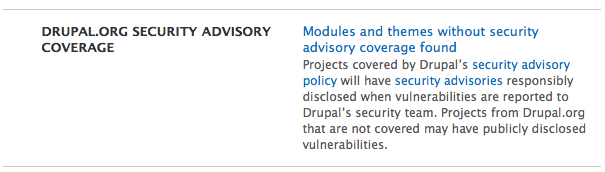
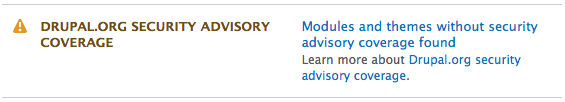
Addition to status report
If everything is covered:

If something is not:
API changes
Theme additions in update module.
Data model changes
We have updated the update status xml to support this change: #2853696: Add security advisory coverage to update status XML and can make additional changes as needed.
| Comment | File | Size | Author |
|---|---|---|---|
| #180 | 2766491-180.patch | 27.18 KB | Akram Khan |
| #179 | reroll_diff_178-179.txt | 1.76 KB | Akram Khan |
| #179 | 2766491-179.patch | 27.18 KB | Akram Khan |
| #178 | reroll_diff_177-178.txt | 9.05 KB | Akram Khan |
| #178 | 2766491-178.patch | 27.2 KB | Akram Khan |












Comments
Comment #2
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedI'm pretty sure yellow is already used for other things (for example, a module that has an update available, but the update isn't security-related). Also, even for a module that doesn't have security coverage, there should still be a way to indicate all the various states that are currently indicated via color: module is up-to-date, module is not up-to-date, module is not up-to-date and a security update is available, etc. So this needs some more thought.
Probably this should try to use something as similar as possible to whatever design comes out of #786702: Add information about releases covered by security advisories to project pages near download table (in order to promote consistency between what people see on drupal.org compared to what they see on their own sites)?
Comment #3
hestenetThat's a good idea.
Comment #5
mforbes CreditAttribution: mforbes commentedWith the new shield icon now deployed on production d.o, I naturally expected to find this thread on adding it to update.module's admin/reports/updates (to use D7 parlance, as I'm not a D8 user yet).
Having the shield on project pages informs about whether or not to install a project; having it at admin/reports/updates would inform about whether or not to keep a project installed. For someone looking to have only covered projects installed, indicators in both of these places would be more comprehensive than just the former alone.
Comment #6
cilefen CreditAttribution: cilefen commentedSo that is a +1?
Comment #7
cilefen CreditAttribution: cilefen commentedI am asking around to find out if this isn't soft-postponed on a theoretical issue to update the XML.
Comment #8
drummYes, the XML needs to have the data before core can show it.
I do recommend getting a head start on implementation here if possible.
The
<release>elements will get a new child with a straightforward value. Maybe<security>covered</security>/<security>not covered</security>Comment #9
mforbes CreditAttribution: mforbes commentedYup.
Something that simple surely makes sense, but is the word "covered" (or variations thereof) already being used in machine-readable places such as d.o's field names and views config? If not, meaning it's merely part of (translatable) strings like the shield's alt text and legend, then we might be wise to avoid it given this explanation of what the indicator really means. It's also worth considering whether or not this will be binary forever. In any case, it should be informed by any machine names that have already been put into use anywhere else.
Comment #10
cilefen CreditAttribution: cilefen commentedThis is as far as I got but I'm quitting for the day.
Comment #11
cilefen CreditAttribution: cilefen commentedWherever we go with styling this, it is to be determined if we simply let the value pass through to the theme layer like this, or update the update status (even adding a new status constant) as it is passed around.
Comment #12
drummActually, a bit of text for the message would be good to include in the XML. Links would be good to be able to use; the text should be otherwise well-sanitized so hacking Drupal.org isn't (more of) a risk to individual sites.
With the D6 end of life, we ran into limitations on what we could communicate via update status, which was not a fun to figure out. See #2687957: Improve Update Status messaging for End of Life in Drupal 7(and Drupal 8 and later).
Comment #13
miwayha CreditAttribution: miwayha as a volunteer commented@drumm: Consider this status message or modules and themes not covered by the Security Team's disclosure policy:
Comment #14
mj-19 CreditAttribution: mj-19 as a volunteer commentedBuilding upon what @miwayha wrote:
Caution: Your site is at risk. Your site uses modules and / or themes that are not subject to the Drupal Security Team's Responsible Disclosure policy. Use of such modules and / or themes may expose your site to security vulnerabilities. For more information see https://www.drupal.org/security-team.
Comment #15
pwolanin CreditAttribution: pwolanin as a volunteer commentedStarting on a test fixture change
Comment #17
drumm#2853696: Add security advisory coverage to update status XML added the data to updates.drupal.org. All XML generated after now will have the new elements. In addition to regenerating after commits on a dev release and making a new release, the whole thing is regenerated daily too. So everything should have the new elements tomorrow.
If the new element contains text, that’s the reason something isn’t covered and should show up in the UI.
<security covered="1"/>means things are good. For example:https://updates.drupal.org/release-history/bad_judgement/7.x
has
<security>Project has not opted into security advisory coverage!</security>on every release.https://updates.drupal.org/release-history/api/7.x
has
<security>Beta releases are not covered by Drupal security advisories.</security>on beta releases.and
<security covered="1"/>on full releases.This helps us with #2687957: Improve Update Status messaging for End of Life in Drupal 7(and Drupal 8 and later) by letting arbitrary plain text in:
https://updates.drupal.org/release-history/api/6.x
<security>Drupal 6 and earlier are not covered by Drupal security advisories!</security>Comment #18
drummThe attached patch builds on #15:
This only shows the information for versions you might want to update to. I think the goal, wearing my security team hat, is to have some indication on the projects you have installed. We could do any of:
Comment #19
hestenet@mlhess, and @drumm, and myself had a call and reviewed this:
- We like the copy from comment #14 for the non-covered releases.
- We'd like to move the shield icon to the left side of the release information to make it more visible.
- We'd like to add the [covered shield] and the [!shield icon for non-covered releases] in the already installed modules list.
- We could use some design work in terms of how to layout these icons and messages in a sensible way - help welcome
Comment #20
drumm(Simple-reroll of #18 for array code style, and being able to apply to 8.4.x today.)
Comment #21
alexpott@mlhess asked me to look at this from a framework manager perspective. There's not much architecture here - I like re-using the shield from d.o - that makes lots of sense. And it'll be good to contrast the security covered modules with those that are not. I definitely think it is worth adding a warning when using modules from d.o not covered by the security policy and #14 looks good in terms of copy. Obviously custom code needs to be excluded. It'd be great to add tests given the importance of putting the shileds on the right modules.
Comment #22
hestenetOne additional element that would be good here is to include the 'You have projects that are not subject to the drupal security advisory policy' message in same kind of warning message like the 'you have modules with security releases' message - that follows admins around the site.
It should be something that can be disabled in something like a settings.local perhaps though.
Comment #23
mforbes CreditAttribution: mforbes commented+1 to #22 given the overall trend that admins should be made aware of a lack of coverage to the same extent that they are made aware of available security updates.
I'm on the fence about that option to suppress the messages though. I suppose that option would suppress both the existing message (updates available) and the new message (not covered). I feel this could lead to an unscrupulous developer, who is at the tail end of a fixed-price contract and had one of these messages just pop up before delivery with no maintenance contract, enabling this option before the client could notice and ask what gives. Then there's an insecure site in the wild, maybe the client has some internal turnover and there's a new custodian who is then also oblivious to this option instead of figuring out that they should get maintenance, etc. etc.
Anyone using such a thing non-maliciously could just as well ignore the messages, instead.
Comment #24
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedI would suggest that a message which appears on all admin pages should be discussed in a separate issue. (That's a pretty big user interface change compared to what was originally proposed here - which is limited to the Update Status report only.)
Comment #25
drummThis patch:
To do:
Tests
Design - I grouped security coverage with up to date status
Copyediting - is everything clearly worded and warnings of appropriate severity?
When uncovered projects are running, add the warning to
admin/reports/statusComment #27
drummThis patch should fix the notices in the last test run and adds either of the following messages to …/admin/reports/status
Personally, I’m not sure we want to put a message on every page. This is important for admins to know, but I’d say it is an order of magnitude less important than running known insecure code, which is the only case we message on every page for admins, that I know of. Conceptually, it is about the same risk, but having an SA with an upgrade to do is a lot more actionable than a project with real potential to have public reports.
Comment #28
hestenetComment #30
drummFixing notices only. Not all the test fixtures have the new XML elements, it is good to test for that case.
Comment #32
hestenetCopy suggestions:
Re: #25
The warning message copy at the top seems good to me.
I think the language next to each module/version is concise and informative.
This is a bit tricky, if I'm looking at a module I already have installed, which is one which does *not* have security advisory coverage on the particular release I'm using - I would find it very reassuring to know whether or not the release being recommend to me does. (As in #18). I don't necessarily need that signal for the 'latest version' and the 'development version' just the 'recommended release' - I think.
Re: #27
I think we might want to adjust the language slightly:
I think the 'Not all modules....' message can probably stay as it is.
Comment #33
drummI shortened up the last suggestion:
This patch also starts adding testing.
Comment #34
drummComment #39
drummI found the bit of changed markup causing the failed test, and added a test for the shield appearing when a project is covered.
Comment #41
drummFixing my failing test.
Comment #43
hestenetAdding tags just to suggest that a designer's eye would be welcome. I think it looks pretty okay - but I'm sure it could be improved.
Comment #44
drummI got the tag added in
ccc_update_test.1_0.xmlin the wrong place in the last patch.Comment #45
xjmI don't think "Needs design review" is actually a thing that anyone looks at, but I think what we actually care about is the usability impact of the design, so tagging for those topic maintainers.
It would be best to put current screenshots in the summary, but #25 and #27 are probably accurate.
Comment #46
xjmFWIW, to me, the black shield icon looks like a bad thing rather than a good one, like it might be a different kind of bad warning like the yellow triangle. But I am not a usability professional.
Comment #47
drummDone, with the issue summary template. And yes, those are current screenshots.
Comment #48
drummI’m happy to change it as needed. I also think some brief explanation to go with the added help text would be good.
On Drupal.org, we use CSS like
filter: opacity(0.5) drop-shadow(0 0 0 #fbf03b) brightness(2);to change the color of the icon to match the background. I don’t seefilter:used outside of 3rd-party things in core; I’m not sure if it is an appropriate level of cleverness for core.Comment #49
ifrikAbout #46
On drupal.org, this shield is grey rather than black when it's part of an explanation. So maybe just changing it to the same grey, would make it look less like a "bad thing" and consistent with d.o.
Comment #50
Bojhan CreditAttribution: Bojhan as a volunteer commentedA few questions:
I would typically use the same color as we use elsewhere (e.g. orange for warning = not covered, red for error = actual security fault) to denote importance.
Comment #51
drummDrupal.org project pages have the shield as a positive thing, I wouldn’t want to reverse this within Drupal installs.
The security team doesn’t really do anything that’s broadly “checking”. We encourage potential vulnerabilities to be reported to us, triage them, and work with maintainers to get a release and security announcement.
Comment #52
mlhess CreditAttribution: mlhess as a volunteer commentedCorrect, the security team does not proactively check anything (as a core function, some team members do)
We already have both positive and negative alerts on this page. I think it would be great to change the page so we only alert to what is wrong, but that is scope creep on this issue.
Comment #53
mlhess CreditAttribution: mlhess as a volunteer commentedDrumm is correct as well, we should match the messaging on D.O.
Comment #54
drummFor security coverage, that actually cuts down the issue by half and solves most of Bojhan’s concerns.
We wouldn’t add the shield, so we don’t need to explain it. On the update status details, we’re only adding the specific alert if something isn’t covered.
Comment #55
DyanneNovaI think it's helpful to have positive notices on the update page. It reassures site administrators that everything is in correct order on their site.
We could take a positive approach to this and use icons to inform administrators of what modules do have security coverage, while educating them in the text as to what a lack of coverage means for them.
I think we can use a shield with a checkmark to convey both "covered and currently believed to be secure" and a shield with an exclamation point to indicate "covered and has a known security vulnerability".
In that case, anything without a shield would indicate that there is no security coverage on the module. Text in bold explains what that means for the uncovered modules.
Here's an example mockup:
Comment #56
hestenetRe: #55
Visually, I think this is a much cleaner implementation. Though I think it goes in the opposite direction of comment #54: showing only positive indicators vs. showing only negative indicators.
So while I like this visually, I'm very much concerned about signaling lack of coverage only through the absence of an indicator (or, I suppose, the bolded text in the example screenshot posted above.) I fear that a user could easily skim past the explanation at the top.
At the same time, I can see how giving the lack of coverage indicator the same visual weight as 'Security update required' could backfire. If a user chooses to ignore the 'lack of coverage' indicator they might unwittingly begin to ignore the 'update required' indicators as well.
Here's one attempt at a middle ground:
Comment #57
Bojhan CreditAttribution: Bojhan as a volunteer commented@mlhess @drumm I am happy to change the messaging on D.O if that needs to match whats here.
Lets take the first step and only warn, when something is wrong. I understand that it feels reassuring, to add it everywhere - but really unsure about the clutter it adds as people won't notice it as much if we have icons scattered everywhere. Honestly even the "up to date" message we have on everything is a lot, but a bit much to change now.
I am not sure about the direction this issue is taking.
Comment #58
japerryOthers can correct me if I'm off base here: But it is pretty important that the status page shows us three things for modules/themes:
I don't really need or want anything else. When we're building sites, most people are making a conscious decision to use a module version and don't really think/care about security coverage. Having a note at the top showing that some modules have additional security coverage is great, but I certainly don't want to see warnings on my site if one of the module versions I use isn't the recommended release. I'm more concerned about active security issues, and not about boogie man theoretical vulnerabilities because a module isn't being watched by the security team.
In fact, I'd go so far to say, if the change was made to comment #54, I'll make a module to disable that functionality. Its a super bad user experience, and gives clients the impression their site is not secure, when that is not the case. I don't think a single Drupal 8 site can use only recommended modules right now, so it'd give the impression that Drupal 8 is not secure.
Comment #59
EclipseGc CreditAttribution: EclipseGc commentedSo, I'll admit, I glossed over this issue, and I know we'll do whatever we're going to do regardless of my opinions however...
Trying to communicate all of this information in a single list seems confusing to me. As a long time member of the community, I understand much of this data already, but if we want someone to visit this page of their site and intuit what's going on, a single list of data is going to be difficult to comprehend. Can I suggest that we might consider leaving the existing list largely alone and adding a new list that communicates exactly which installed modules are not covered by the security team? That would, imo, communicate much more clearly and concisely about the two different sets of problems we're trying to tackle without conflating them together.
Just a suggestion. Carry on.
Eclipse
Comment #60
DyanneNovaAfter looking at this more, I noticed that we already have a pattern for this kind of information in core with experimental modules.
Instead of adding extra information to the Updates page, why don't we list all of the modules that lack security coverage under a warning on the Status report page?
That gives the user a clear alert as to the potential problems, lists all of the modules with that issue, and follows a current ux pattern we have.
Comment #61
drummSee “Addition to status report” in the issue summary, and #27. Currently, it is linking over to the update status page. We could have it list the non-covered modules out right on the update status page.
The ability to configure away these warnings has been tossed around.
Comment #62
drummThis patch adds the specific modules not covered to the status report page:
The text for each module is from updates.drupal.org and can be revised at any time as we change/clarify policies, or learn how to copyedit.
I’ve left in all the work on the update status page for now. We need to decide:
I’ll continue work on this to add tests as we get clarification. And a settings.php configuration to ignore the warnings.
Comment #63
DyanneNovaI think we can remove the explanations for the lack of coverage on the warning and instead explain on the security advisory coverage document that Dev and RC releases aren't covered. That cuts down on redundant messages for the same information. I'm not sure that users need the release information. If they choose to update to a release with security coverage they'll likely need to do much more research to understand what their options are.
That would make this look a bit closer to the Experimental Modules warning, like this:
Modules or themes without security advisory coverage found: Drupal core, Devel, Token. Learn more about Drupal.org security advisory coverage.
I think that's enough without changes to the updates page. It gives the site admin a warning when they check their status. It tells them what modules or themes are at potential risk, and gives them a link to more information about that risk and what they can do to improve the situation.
Comment #64
hestenetUpdating the issue summary to more clearly state the implementation questions that have been asked and still need to be resolved.
As we continue to work here in the issue, I have also reached out to the @yoroy on the Usability team to see if the DA and members of the Security Team could join one of the upcoming Usability meetings to hash out answers to these questions (or set up an independent call if needed.)
Comment #65
drummThis patch adds the killswitch to
settings.php:I’m also updating the issue summary with an additional example installed, to show another way a release might not be covered.
Layout plugin currently hasn’t opted into the security advisory policy. (This is somewhat equivalent to running a sandbox project for security coverage.) The maintainers can make a 8.x-1.0 release without any change in coverage.
I agree the messages are repetitive, we can change them, but I do want to offer some explanation of why exactly a specific project isn’t covered without sending people to figure it out for themselves.
Comment #66
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedNormally when there is a warning in the Status Report, we also provide instructions to site administrators on how to fix the problem.
What would the instructions say in this case? All I can think of is "uninstall the modules", but that seems like a very disproportionate and unrealistic solution for most sites...
For that reason, I'm not sure that a warning message in the Status Report actually makes sense here.
Comment #67
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedI think the actual message we're trying to get across to site administrators is something like this:
"The system is not able to tell you whether these modules have known security issues or not"
That manifests itself in two ways:
I'm not sure how to express the above via a graphical icon... but something like a shield with a question mark inside it comes to mind?
Comment #68
yoroy CreditAttribution: yoroy at Roy Scholten commentedAlthough this is not necessarily an optional idea I think it would still be helpful to get answers to the 4 questions we ask when reviewing core ideas:
What is the problem to solve?
(Missing functionality X, prevent Y from happening, make Z easier to do)
Who is this for?
(Evaluators, site visitors, content authors, site managers, (advanced) site builders, frontend developers, backend developers, core developers, site owners, other?)
Result: what will be the outcome?
(Describe the result: how will this improve things for the stated audience(s)?)
How can we know the desired result is achieved?
(Usability test, a metric to track, feedback)
I'm especially interested in 3 and 4: what positive change are we aiming to achieve and what could we track to measure if that's what's happening?
Comment #69
drummGood questions - I added answers to them to the issue summary.
Comment #70
hestenetComment #71
hestenetComment #72
hestenetComment #73
hestenetComment #74
hestenetToday (April 18th at 12pm PST) we had a call with the UX team, DA Staff, and members of the Security Working Group to help sort out some final implementation questions for this issue.
We made the following decisions:
(these first three could perhaps be a single column?)
We need design work to figure out what the columns/background colors/iconography should look like, and we should do a comparison of the accepted design to Drupal.org's own security signals and pull in those changes to D.O as well for consistency where appropriate.
Comment #75
yoroy CreditAttribution: yoroy at Roy Scholten commentedLink to the recording: https://www.youtube.com/watch?v=Q7JuMD2rrm4
Comment #76
phenaproximaI have a question here, although it may be out of scope -- our minimum version of PHP for Drupal 8 is still 5.5.9. Which is way beyond its end of life, and no longer receiving any security fixes. And yet, our status page does not warn about that at all. Why not?
IMHO, the current generation of the patch (as seen in #65) is too strong. I don't think this should be a warning. I don't even think it should include exclamation points. It should be a notice -- a thing to be aware of, if you care to know. We should be critically careful not to scare the hell out of the people who will be using non-covered modules (which might include custom modules and forks), which I'm guessing will be the overwhelming majority of even mildly complicated Drupal sites.
Comment #77
ohthehugemanatee CreditAttribution: ohthehugemanatee as a volunteer commentedThis is very important, especially to encouraging security coverage status in contrib modules.
The devil is in the details - just how scary and intrusive the warnings are. Too intrusive, and site maintainers will ignore the really critical stuff, because "those messages are always there." Not intrusive enough, and we won't pressure maintainers into SA coverage. In the worst case, we'll have module maintainers marking unstable code as 1.0, just to silence the warnings for their users.
Part of the problem is that we don't have any kind of intermediate error status available. Just errors (fatal), warning (action item that must be resolved), and informational. Almost every site will have to ignore this warning, if they use:
* custom sandbox modules
* a dev/alpha/beta module
Has anyone on this thread EVER built a site without any of these?
It's also a laughable comparison to the things that we DON'T warn about:
* patches, even core patches, even core patches that aren't sourced from d.o issues
* known insecure PHP versions
* known insecure library versions
There is an important difference between "this isn't subject to a responsible security disclosure process" and "this has a known security issue". One of these messages will occur on a majority of Drupal sites, and people can choose to ignore it dependent on their context. The other one of these messages is a serious warning that should block a site launch. If we don't differentiate, we are stuck either over-emphasizing one message, or under-emphasizing the other.
Comment #78
japerryFirst, lets identify what a 'warning' is on the status page. These are (or should be) actionable items that a site builder can take to eliminate said warning on their site. But this warning (as well as experimental modules) has no immediately actionable item, except tearing their website down to only full releases, covered by the security team. While it'd be great to think we could use these warnings to push for stable releases, the simple fact is, it won't. This issue reeks of politics (throwing a 'bone' to the security team for the project application process) and not a solid UX or technical implementation.
However, I agree that somewhere on the status page, as a notice, would be a good place to mention if the site contains modules that aren't part of security coverage. This could be a link to a page on the site listing the modules, or a page on drupal.org that goes into the nuance about security coverage.
No, security coverage should not be mentioned here at all. The update status page is to be about updates and known security updates, nothing else. Security coverage doesn't fall under this, pollutes the update page, and unnecessarily will scare users.
Its also important to know that the decision to choose a module is where this messaging should be, not a constant nagging. I support (for the most part) the current messaging on drupal.org, and would suggest making a way to warn builders before enabling a module not covered by the security team.
two more issues that should be addressed before this issue moves forward
This issue is extremely important to get right. If it is done wrong, the community will make a contrib module to revert this change.
Comment #79
hestenetI absolutely agree that good UX design is critical to this issue. That is why we had a meeting about this with as many stakeholders as we could pull together on April 18th, hosted by the UX team.
#74 summarizes the minutes from that meeting with the UX team. And #75 has the recording if you'd like to view that.
I hear the fundamental concern very clearly: Don't scare users away from using Drupal. That was very much a topic of conversation during that call, and nobody wants that.
The decision-tree/check-boxes outlined in the "Implementation questions..." section of the issue was filled out collaboratively during that call.
However - please note that the current mocks and current patch do not represent the outcome of that call. We haven't had a chance to roll a new patch, and we were hoping for a new round of design mocks to work from. (I believe @dyannenova was going to work on new mocks if she has the time to do so- maybe we can sync up during Baltimore sprints?)
To address a few of the recent comments:
#76
#77
#78
I think the last call on this issue with the UX team was very productive, and I'd encourage folks to check out the recording for some of this discussion.
I'm hopeful that the next set of design mocks can strike accomplish the goal of being informative without being frightening.
Comment #80
fuzzy76 CreditAttribution: fuzzy76 commentedI actually think that the warnings _should_ be scary. Running alpha/beta in production is a dangerous thing. The real change that would / will fix this is that maintainers need to actually push stable releases more often and stop leaving their modules in beta for five years. And if they get more complaints from users because of this, it might actually happen.
Comment #81
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedBut again, what is the "action" in this case?
There is nothing they can do from the updates page to make the warning go away -- and nothing realistic that they can do at all to make it go away. See my comment in #66, and @japerry makes a similiar point in #78.
These are big changes that seem out of scope for this issue, and (more important) I'm worried they would put way too much focus on the security coverage status information. The security coverage indicator should not be as prominent as the up-to-date indicator, but this design change would tend to make them equally or almost equally important.
Also, these changes seem like they would directly contradict Bojhan's concerns from #50:
I think that putting this info on the update status page does make sense (I disagree with @japerry on this, for the reasons I mentioned in #67) but it should be a simpler change that just adds a small bit of information to the existing design.
I agree with the conclusion, but don't understand the reasoning :) The "there are issues with this site" message only appears in the admin interface if there are errors with your site, not warnings (which is what you are proposing to add).
Comment #82
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedI really suggest considering a simpler design, such as the one @hestenet posted in #56 (bottom panel only). I'm copying a version of that cropped to the bottom panel here:
The text is probably too long (could just use the first sentence, or even something shorter like "No security advisory coverage"?) but in general I think this is the kind of change we're looking for in this issue. And it could use the same design regardless of whether the project has updates available or not.
Projects that do have security advisory coverage don't need an indicator at all, as others have said above -- it doesn't add any particularly useful information. Yes, it is true that this would sort of be the opposite of drupal.org (which shows positive indicators for releases that have security coverage) but I think that's fine, since the purpose is different. The drupal.org pages are primarily designed for people who are installing new projects, so it makes sense for the icons to guide them to the "correct" thing to download. The Update Status page, however, is designed for people who already have the project installed on their site, so it makes sense for the icons to highlight cases that require extra attention.
Comment #83
yoroy CreditAttribution: yoroy at Roy Scholten commentedWe initially discussed a table based approach with additional columns but I couldn’t make it work.
1. Changed to a “box per module” design. The table-based approach isn't really up to fitting all the different types of things that we need to show per project
2. Moved the "Includes" bit right below the module name
3. We currently have two links to release notes, one to download. I removed the explicit "relase notes" link per release. Clicking the module version link gets you there as well.
4. The security coverage info is shown as a short sentence with a link. I left out the icon so that there's no competition with the actual status info icons.
5. I didn’t look into use of color to indicate status. I'd eventually like to see color used more sparingly than the current full row background fills.
What did I miss? :)
Comment #84
yoroy CreditAttribution: yoroy at Roy Scholten commentedComment #85
japerryAdded a somewhat related issue.. where hopefully we'll be patching core soon to eliminate the experimental module warnings.
Looking at the screenshot #83, we see redundant , inactionable, text. As a site maintainer, what am I going to do with this? Its really unfortunate that we aren't instead showing some positive wording instead that shows which modules are covered by the security policy. Maybe even order them at the top or something.
Comment #86
yoroy CreditAttribution: yoroy at Roy Scholten commentedI *knew* I messed up something :)
I'm fine with switching this to positive messaging and labelling the projects that *do* have coverage. Then we'd have to match the messaging on Drupal.org as well. (Projects without any covered releases could then still have the 1 single warning)
Happy to revisit this, but so far did not get feedback on the overall proposed design.
Comment #87
drummAttached is a patch bringing in feedback summarized by #74, #83, and #86.
The new warning on the status report page:
Project-specific details have been removed.
The updated updates status page:
admin_blocktheme function, which comes with the light grey background.Comment #89
japerryLooking better! However, I'm still going to strongly argue that having the missing security coverage piece being a warning is too much for site owners, because warnings are supposed to indicate something that is actionable/fixable. This does extend to experimental modules as well, which also has too strong of wording and should be informational, unless we can find something better (suggestions maybe?)
But lastly, and maybe most importantly: My site is telling me that those who developed the site have done something potentially wrong. Along with the experimental modules (in which layout discovery should definitely be used right now, and is experimental for bad reasons IMHO), we cannot have sites contradicting what are considered module best practices within some of largest drupal development agencies in the world.
In a few years, this might not be a big deal. But right now, in Drupal 8, we cannot have warnings like this on the status page, because they are just plain misleading.
Alternatively, similar to experimental modules, I do think having some stronger wording during install is a good idea. Its important that site builders understand the potential ramifications of installing experimental and/or pre-release modules. But once the architectural decision is made, there is little reason to keep bugging the admin/user/future user about it...
Comment #90
hestenetI'm glad to see we're closer to consensus here.
I think @DyanneNova's reasoning in originally suggesting the warning message on the status page is sound. #2766491-63: Update status should indicate whether installed contributed projects receive security coverage
Also - it is incorrect to say that the message is not actionable.
While the message is not always actionable it may be actionable for some number of sites and users.
I'm sure one could quibble with some of these scenarios - but the point is there are sites out there that are not the big enterprise sites with ready support from big shops/dev teams - and there are any number of ways that these sites could wind up with non-covered modules when that information is actionable.
And in all cases there's the minimum action of simply being aware of the risks of public disclosure. I think the current patch in #2766491-87: Update status should indicate whether installed contributed projects receive security coverage accomplishes that without being overly frightening.
I'd really appreciate another review by @yoroy, but I think we're close to RTBC.
Comment #91
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedThose might be reasons for an informational message, but not a warning message. (Especially since the new design doesn't treat this as a warning condition on the Update Status page itself, just an informational condition there - why would we then go ahead and treat it as a warning elsewhere?)
I think discussion of a message on the Status Report, as well as of a confirmation message when enabling modules (from #89), would be better off discussed in a separate issue anyway.
***
As for the message on the Update Status page, it looks pretty good. However, I'm concerned that many of the changes are unrelated to this issue and not necessarily a good idea. We should not be changing things that don't need changing here, especially in Drupal 7. Two things in particular:
Why? This is taking the least important information and putting it near the top. This seems especially bad for Core (which as can be seen in the screenshot from #87 has a very long "Includes" list) because it pushes the important information way down to the bottom.
I am concerned that no one will know that though. Personally I've always clicked on "Release Notes" myself, and I think there is some logic in having it as prominent as the "Download" link. Was the goal here to save space given the new "Covered by" text that's being added? Is there another way we can deal with that?
Comment #92
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedComparing the overall before and after screenshots (see below) this really doesn't feel like an improvement to me. The "after" screenshot (a) has way fewer visual cues to tell you which modules are up to date and which aren't (due to the removal of the background colors) and (b) has lots of extraneous text (including the "installed version" text plus the release date on an already up-to-date module, which doesn't seem useful to me and wasn't in the design either).
Again, I think it would be better to try to make the smallest possible changes that can be made to get this issue fixed.
Comment #93
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedMy previously-uploaded screenshots (in the above comment) were bad so here are better ones.
BEFORE:
AFTER:
Comment #94
yoroy CreditAttribution: yoroy at Roy Scholten commentedThanks for a more detailed review @David_Rothstein :)
I would prefer to agree on the different kinds of changes needed in this issue. Implementing and fine-tuning a warning on a confirmation screen can be a separate issue. Deciding we want to do that in the first place, that would be good to do in here.
In general I reshuffled things because there are potentially quite a lot of different things to communicate per project/release. I don't think we can just append another line of text to what's there now. Doing the minimal change here would amount to simply adding yet another line of text to each release. I feel we should and can do better than that.
Remember that my proposal was a wireframe. I think we're missing a visual design treatment because without the color coding and other queues the current patch makes things less quick to scan indeed.
Comment #95
japerryI did a little bit of investigation to see how the Experimental warnings UX came to be. Turns out, there was no UX or really any community review other than Alex and XJM. So I don't think we should be relying on that UX as a good idea. In fact, I've suggested we remove it: #2880374: Experimental modules and themes should not have warnings after being installed
Disagree pretty strongly about those reasons for 'actions':
Here is an example screenshot of what we could see for typical warnings pre-launch of a site:
You'll see something familiar here, all of these, except experimental modules, are reasonably expected to be actionable I do not consider uninstalling a module a reasonable action.
Comment #96
japerryComment #97
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedOK, can everyone here agree on an informational message on the status report page, rather than a warning message? (That is what #2880374: Experimental modules and themes should not have warnings after being installed proposes for experimental modules also.)
That works for me. I would not be surprised if someone complains about it, but I am OK with it myself :)
Hm, well I guess the wireframe was implemented in the patch... But if it was just supposed to be a wireframe, then yes, that makes more sense.
Comment #98
drummWorks for me too. Occasionally release notes pages have useful notes. Sending people to them is okay.
This patch makes that change and cleans up the tests. There are no visual changes for now.
Clear messaging was strongly requested from the security team point of view. For now, I left it as-is. We can wait and see where #2880374: Experimental modules and themes should not have warnings after being installed goes.
Comment #99
drummForgot to set the status for testing.
Comment #100
yoroy CreditAttribution: yoroy at Roy Scholten commented@ifrik and I discussed another possibility, which is grouping the projects in "covered" and "not covered" buckets on the page. This way it's not necessary to mention this information for each module.
Here's a more refined *wireframe*. I put the background colors back in:
Comment #101
yoroy CreditAttribution: yoroy at Roy Scholten commentedComment #102
yoroy CreditAttribution: yoroy at Roy Scholten commentedThinking about this in terms of minimal viable changes we can make. The goal of this issue is to indicate which modules are covered by the security advisory and which ones are not. This is important information but repeating it for every listed *release* of a module would mean adding a lot of repetitive text to the page.
So:
1. Must have: Group the modules that have available updates into 2 main buckets: covered and not covered. We'd still have to design how each of those headers look. But even when we'd leave the current table based display as is, this change alone would fulfill the must-have issue goal of indicating security advisory coverage.
2. The could-have would be to move away from the table based display and have boxes per project.
3. The nice-to-have then is to rearrange the information and links within each listed release.
I'm curious to hear whether people would agree with these priorities. If so, we can then design and write the specifics for the covered/not covered headings. This diagram draws a box around each of the two buckets but not sure that's actually necessary in the visual design.
Comment #103
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedI like that change when considered in isolation.
But there are opportunity costs to breaking the page up into those buckets. If you're moving away from a plain alphabetical listing, are those really the best buckets to use? Why not group by a more important attribute instead? (For example, putting modules that aren't up-to-date, and that have security updates which need to be applied, at the top of the page would probably be more logical - and would correspond more closely to how other pages such as the Status Report page at admin/reports/status are grouped.)
If the goal is just to reduce the repetitive security advisory text, shortening the text could be a simpler way to accomplish that... something like "Has security advisory coverage", for example.
Comment #104
drummThis is a work in progress, only #98 with bringing back the background colors for security update status. (Security advisory coverage does not affect the background color.)
Depends on #2887860: Allow attributes to be passed to admin blocks (admin_block theme hook). This patch replaces table formatting with
admin_blocktheming. The table had been a single column without headers, it wasn’t really being used.Comment #105
drummThis was done on or before #98. The copy shown, as you can see in the issue summary screenshots, is “Covered by Drupal’s security advisory policy”
The update status page with this patch has no information about the real risks of running non-covered releases.
Comment #106
drummThis information is per-release. For example, if your site has 8.x-1.0-beta3, with an upgrade to 8.x-1.0 available, that upgrade would bring your site into more security advisory coverage. Doing that upgrade might be nearly as important as an upgrade for a security announcement.
https://www.drupal.org/project/media/releases/7.x-2.0 is an example of this happening recently. That release had security improvements, but as the first stable release in the 7.x-2.x series, no security announcement was required.
Comment #107
drummReplacing the update status screenshot in the issue summary with the version from #104 with background color.
Comment #108
drummFixing a bug where the installed version sometimes was not shown. Otherwise, equivalent to #104
Showing the installed release information had been simply showing the version string. It is now using the full data structure to match the “Recommended version/Security update/etc” options below. But, I missed a place where
update_calculate_project_update_status()needed to be sure to pass on the installed version’s release information.Comment #109
drummOn grouping the page - we should make sure the update status page always highlights available updates, security and otherwise.
Lack of security advisory coverage is important too. Those updates will include security fixes that aren’t called out by a security announcement. And the public issue queues for those projects will have security issues without fixes. Even if there isn’t an actionable upgrade, there is risk you should be aware of, or paying someone to be aware of.
That said, grouping by covered/not doesn’t seem like the right approach. That seems like it is prioritizing that above updates available.
Comment #110
drummAdding
use Drupal\update\UpdateManagerInterfacefor the class constants for coding standards.Comment #111
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedMy intention was to shorten it further. The difference is only a couple words, but every word counts... I feel like this is something I learned from @yoroy at some point :)
Comment #112
yoroy CreditAttribution: yoroy at Roy Scholten commentedOk, if grouping by status is not viable then we add the information to each release. In as few words as possible :)
Comment #113
ifrikAgreed - at this stage it is more important that users are aware whether modules are covered by the security advice or not. So the minimum viable change is to add that text to the page as it currently is, even if it's repetitive or doesn't look pretty.
Let's provide that information to users now - and change the display once somebody comes up with a good idea.
Related issue: the Help text for the Update module then need to be changed, to mention this additional information under "Checking for available updates"
Comment #115
drummRebasing for 8.5.x
Comment #116
drummMinor update to keep up with a change in #2887860: Allow attributes to be passed to admin blocks (admin_block theme hook)
Comment #117
larowlanBlocker is in, so may need a re-roll here?
Comment #118
drummNo re-roll needed. My local branch rebased cleanly.
Comment #119
hestenetAfter most of a month with what looks like consensus, and some good stand up conversations here at DrupalCon Vienna saying "go for it!" I'm going to be brave and mark this RTBC!
Thanks all.
Comment #120
yoroy CreditAttribution: yoroy at Roy Scholten commentedAgreed, go for it!
Comment #121
David_Rothstein CreditAttribution: David_Rothstein as a volunteer commentedA couple people have discussed above why a warning on the status page is not appropriate here. (Also, it's confusing - it points you to the update status page to look for projects that don't have security coverage, but the update status page only labels ones that do (and doesn't distinguish between ones that don't and ones that are non-drupal.org projects where it isn't relevant).
I think it would be wise to just remove this warning and leave it for a followup issue... but if not, can we at least switch it to a REQUIREMENT_INFO (as discussed above) and make it more informative, rather than like a warning?
Also, I do not think there should be a switch for turning this off in settings.php. That is just a crutch for not being confident that this message is actually useful for real-world sites. We should either have a message that is useful, or not have one at all.... "Decisions, not options", as they say in the WordPress world :)
Why are some of the previous error conditions no longer being treated as errors here?
What happened to the apostrophe in "Drupal's"? (Same issue other places in the patch too.)
I agree this is worth considering.
If 8.x-1.1 is a security release, then is 8.x-1.0 really "covered by Drupal’s security advisory policy" (as labeled in the screenshot)? I think the technical answer is "sort of", but I also think many people would be really confused by this. I would suggest removing the label from all but the most recent security release in this scenario.
Second, some general issues with the design visible here are (1) the "Security update" is not well-highlighted compared to the "Installed version" (I think it's more difficult for people to quickly see what the required action here is than it is with the current design in core), and (2) I still think the "Includes" line is in too prominent of a place. Suggestion: Could "Includes" be moved back down to the bottom (where it previously was) and could "Installed version: 8.x-1.0 (2017-Apr-01)" (all on one line) be moved to where "Includes" is in the screenshot? I think that would do a better job differentiating the current installed version from the recommended updates.
Comment #122
Bojhan CreditAttribution: Bojhan as a volunteer commentedRemoving tags. Yoroy has reviewed this through and through.
David's concerns should be addressed, but seem quite wholesome - it would be worthwhile to jump on a call.
Comment #123
drummThat is a manifestation of #2922638: No charset on response for patch & text files. I’ve gotten in the habit of curly quotes in text for humans, and don’t think I’ve run into problems outside of the browser.
Comment #124
drummUpdated patch for David_Rothstein’s feedback is attached. I think I have everyone’s feedback taken into account now. Screenshots in the issue summary have been updated.
Ok, done. The message is now more informative:
Projects covered by Drupal’s <a href="https://www.drupal.org/security-advisory-policy">security advisory policy</a> will have <a href="https://www.drupal.org/security">security advisories</a> responsibly disclosed when vulnerabilities are reported to Drupal’s security team. Projects from Drupal.org that are not covered may have publicly disclosed vulnerabilities.Also done.
Fixed, this was an oversight in refactoring away from deprecated global constants.
Added this copy in both admin/help/update & admin/reports/updates:
Projects covered by Drupal’s <a href="https://www.drupal.org/security-advisory-policy">security advisory policy</a> will have <a href="https://www.drupal.org/security">security advisories</a> responsibly disclosed when vulnerabilities are reported to Drupal’s security team. Projects from Drupal.org that are not covered may have publicly disclosed vulnerabilities.I’d say yes, it is covered, it got a security announcement.
I did some rearranging based on your other feedback (see screenshot in issue summary):
Comment #126
drummUpdating tests for a copyediting change I made: “Recommended version” → “Recommended update” to match “Security update”, which reads a bit better for me.
Comment #127
hestenetAfter the latest changes I think we're RTBC again.
Comment #129
drumm#128 was a spurious DrupalCI failure.
This version fixes the coding standards issue, removing an unused use statement.
Comment #130
larowlanWe can't backport this to 8.4 because of the string changes, so removing that tag.
Comment #131
larowlanlogic that checks a class feels wrong.
What if someone adds an additional class name or changes the classes via preprocessing.
We should be adding a new variable via template preprocess here.
I've tagged for front-end framework manager review, as there are quite a few front end changes here.
Comment #132
joelpittetIt's wrong in a couple ways, but mainly it assumes one class: use
{% if not attributes.hasClass('project-update__version--installed') %}Passing in purposeful variable may be better though as mentioned in #131
Comment #133
joelpittetAlso, we should try to avoid name changes because people could be trying to extend the templates in their own admin themes, so changes in stable/classy like 'table' to 'content' keys can do a lot of BC damage.
Comment #135
drummThis patch addresses #131 & #132. A new
typekey is added to theupdate_versiontheme. It can be used to determine if the version being rendered is the one already installed, or a few more types of versions that might be shown.It is also rebased against 8.6.x.
Comment #136
drummRe #133: the contents of
tableandcontentare both render arrays to represent a set of projects. Before this patch, it uses basictabletheming; the replacement is an array ofadmin_block, no longer literally a table.I could see going either way on this - the replacement is still a render array, but the “table” name is starting to rot.
Comment #137
hestenetGoing to give this another try and see if we feel ready to go here. :)
Comment #139
drummTest failure was due to DrupalCI system issues.
Comment #140
larowlanThis still needs frontend framework manager review for the changes to stable templates, I'll ping @lauriii
Comment #141
lauriiiSorry I don't have a chance right now to give a full review but I want to post my initial thoughts so that we can try to move this issue forward.
We shouldn't use type as a variable name for templates since it is one of the render array keys that has special functionality attached to it. More info https://www.drupal.org/docs/8/api/render-api/render-arrays#properties
What happens if value is not provided?
Comment #142
drummThanks for the review, laurii.
Renamed to
version_typeAll uses of this template have been updated to provide a value. I expect this is not used outside of core. The addition to
update_theme()gives it aNULLdefault.Done. I also renamed
contentback totable, as recommended in #133 to make this work well.Comment #144
drummThe reverts to stable changed what testing hits, reverting parts of that to match.
I also removed an extra
clearfixclass that had been added to make a previous design work. It is no longer needed and keeps testing more consistent.Comment #145
lauriiiThis seems like an unnecessary change. I agree that this would make sense, but this will break any potential overrides of the template. I'm happy with the patch once this gets fixed so removing the tag.
Comment #146
drummThat actually is reverting a change in earlier versions of the patch. The
tablekey no longer makes sense, but it is being kept consistent so existing templates have no necessary changes.Comment #147
LaravZ CreditAttribution: LaravZ commentedA minor issue: I'm seeing the text "Covered by Drupal’s security advisory policy" displayed on the update status page. It does not seem to be converted properly.
Comment #148
drummThat is a symptom of #2922638: No charset on response for patch & text files. If you are using a browser to download patch files, you can manually set the text encoding under the View menu. Downloading patches with
curlorwgetavoids the issue too.Comment #149
LaravZ CreditAttribution: LaravZ commentedaha, makes sense, my bad. I did not encounter any other problems.
Comment #150
hestenetGoing to be brave and RTBC this again!
Comment #151
xjmSo there's lots of stuff in this patch that's not strictly a part of the same scope, like changing the usage of the old update status constants to the class constants, changing the string labels, correcting an incorrect test assertion message, visual changes, etc. It would be better to split these different changes into different issues so that we have the minimum changes needed for each.
This also need to be wrapped at 80 characters. :)
Comment #152
xjmComment #153
xjmBTW, @hestenet, it'd be best to only mark the issue RTBC if you're actually doing reviews of it. :) And if you are doing reviews, please document what you reviewed and how. :)
Comment #154
drummAdding a note about
_update_equivalent_security_releases()to the issue summary. This issue is not the non-temporary fix to replace that function.Comment #156
xjmThe documentation for
_update_equivalent_security_releases()was fixed awhile ago, so removing that note from the top of the page.Also retitling to avoid similar confusion in the future.
Comment #157
xjmComment #158
xjmCan we get some recent screenshots of this issue? IT'd be useful to see what elements of the proposed designs have been incorporated, and how the current patch compares. Thanks!
Comment #159
drummI believe the screenshots are updated, unless there are other changes to update status that have been committed in the meantime.
I don’t expect to have more time to dedicate to this issue in the near future.
Comment #166
cilefen CreditAttribution: cilefen commentedThis needs a reroll to proceed.
Comment #167
karishmaamin CreditAttribution: karishmaamin at Specbee commentedRe-rolled against 9.4.x
Comment #168
xjmCould we add the shield icon before the coverage message, to match d.o? I feel like there's not quite enough visual differentiation as-is.
Comment #169
ranjith_kumar_k_u CreditAttribution: ranjith_kumar_k_u at Zyxware Technologies commentedFixed CS errors.
Comment #170
ranjith_kumar_k_u CreditAttribution: ranjith_kumar_k_u at Zyxware Technologies commentedComment #172
cilefen CreditAttribution: cilefen commentedI am referencing some similar efforts.
Comment #174
Medha KumariReroll the patch #167 with Drupal 9.4.x
Comment #175
pooja saraah CreditAttribution: pooja saraah at Srijan | A Material+ Company for Drupal India Association commentedFixed failed commands on #174
Comment #176
nod_D10 version needed
At this time we need a D10.1.x patch or MR for this issue.
careful reroll
The patch can be tricky to reroll and some code might get lost in the process. When rerolling this issue please make sure all the parts of the patch are kept (new files, new tests, all the changes to the different parts of the file, changes to es6 files ported to .js files, etc.)
Commit check failures
The last patch doesn't pass commit checks, could you make sure to run
./core/scripts/dev/commit-code-check.shbefore uploading a patch to make sure there are no issues with code formatting. see https://www.drupal.org/docs/develop/development-tools/running-core-devel...Thanks!
Comment #177
Nitin shrivastava CreditAttribution: Nitin shrivastava at OpenSense Labs commentedtry to fix CCF ERROR #175
Comment #178
Akram KhanFixing CCf #177 and Upadting patch against 9.4.x
Comment #179
Akram Khantry to fix CCF #178
Comment #180
Akram Khan