Closed (fixed)
Project:
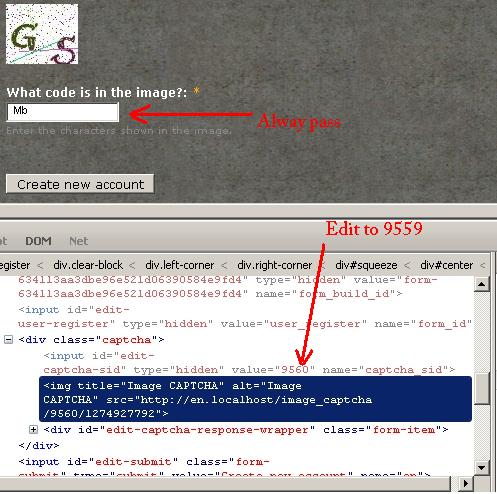
CAPTCHA
Version:
8.x-1.x-dev
Component:
Captcha API (captcha)
Priority:
Normal
Category:
Bug report
Assigned:
Unassigned
Issue tags:
Reporter:
Created:
27 May 2010 at 02:52 UTC
Updated:
24 Jan 2017 at 12:04 UTC
Jump to comment: Most recent, Most recent file


Comments
Comment #1
72ls.net commentedAdd image
Comment #2
soxofaan commentedConfirmed,
It's even worse: you don't have to fill in a CAPTCHA answer, just changing the session ID is enough to pass
This is pretty serious and unfortunately I don't have the time to look deeper into this today.
Comment #3
72ls.net commentedThis is my temp solution. Hack code
File: captcha.module
Function: function captcha_validate($element, &$form_state)
Line: 515
If it's good, pls let me know :)
Comment #4
soxofaan commentedThe hack in #3 will cause problems on forms with previews and other multipage forms I'm afraid
Comment #5
72ls.net commentedthanks
my site was disable previews mode and have no multipage form, but I'm still waiting for your upgrade, thanks again
Comment #6
soxofaan commentedHere is a first shot at it.
This patch should fix it for forms like comment. It doesn't work for node-add forms with preview however (testbot should see this)
Note: this patch adds a column to the captcha_sessions table, so be sure to run update.php after patching (or do a fresh install)
Comment #8
finex commentedsubscribing
Comment #9
soxofaan commentedFYI:
I just made a patch for #773124: CAPTCHA dissapears after correct anwer, even with persistance "Always add challange". This is a feature request for a true "always add a challenge" persistence. When you use this persistence level, the CAPTCHA session reuse hack should not work.
This could be used as a temporarily workaround for the problem.
Comment #10
rob_roy commentedThe same 'hacks' are possible using the basic 'math' captcha !
I have a site using Webform with Captcha enabled where multiple automated submissions of complete nonsense text have been submitted over a couple of days on an infrequent time scale ie the Captcha module appears to have been bypassed.
Could this 'hack' result in multiple automated submissions ? Confirmation or otherwise appreciated before I look for other possibilities as cause.
I have installed the patch #773124 as suggested and run update.php but the 'hack' is still possible.
Thank you in advance
Comment #11
finex commentedI confirm that in the last days spambots are doing a good job filling out contact forms :-(
Comment #12
soxofaan commentedabout #9:
Just committed fix for #773124: CAPTCHA dissapears after correct anwer, even with persistance "Always add challange", so it should be available in 6.x-2.x-dev snaphot when it becomes available (within 12 hours at most).
Re #10: the workaround is to
install the patchinstall a 6.x-2.x-dev from June 12, 2010 or later AND enable the "always add a challenge" persistence option. See attachment for visuals.On my setup it breaks the hack (session can not be reused).
Comment #13
soxofaan commentedThis patch should pass testing
Comment #15
soxofaan commentedthis patch should pass testing
really :)
Comment #16
soxofaan commentedfurther tweaking of fix: added simpletest coverage of the problem and its solution
(also a bit of simpletest refactoring for better code reuse)
Comment #17
soxofaan commented(Further tweaking of the fix.)
To all people in this thread: please test this patch (make sure you run update.php, because there is a database update).
This is a pretty major change in the module and I wont commit this without some more serious testing.
I tested it myself, mostly through implementing simpletest coverage test cases (with comment form, node form and user login form), but I'd like more real user tests from you guys and gals.
So if you want this fix in a official release as soon as possible: please give it a try and report your experiences.
Comment #18
rob_roy commentedBit of a noob to the patch process so please forgive this simple question !
MAC OS x 10.4.11 captcha 6x_2.2
uploaded patch to captcha directory and logged into directory via ssh and ran command patch < 810534_session_reuse_hack_05.patch
However log returned
idesigner.co.uk@n10:~/domains/dev.idesigner.co.uk/html/pragmedic/modules/captcha$ patch < 810534_session_reuse_hack_05.patch
patching file captcha.install
Hunk #2 succeeded at 274 (offset -21 lines).
patching file captcha.module
Hunk #1 succeeded at 182 (offset 10 lines).
Hunk #2 succeeded at 214 (offset 10 lines).
Hunk #3 succeeded at 437 with fuzz 1 (offset 10 lines).
Hunk #4 succeeded at 462 with fuzz 1 (offset 10 lines).
Hunk #5 succeeded at 483 with fuzz 2 (offset 9 lines).
Hunk #6 FAILED at 512.
1 out of 6 hunks FAILED -- saving rejects to file captcha.module.rej
patching file captcha.test
Hunk #1 succeeded at 14 with fuzz 2 (offset -1 lines).
Hunk #2 succeeded at 157 (offset -1 lines).
Hunk #3 succeeded at 167 (offset -1 lines).
Hunk #4 succeeded at 210 (offset -1 lines).
Hunk #5 succeeded at 218 (offset -1 lines).
Hunk #6 succeeded at 278 (offset -1 lines).
Hunk #7 succeeded at 306 (offset -1 lines).
Hunk #8 succeeded at 322 (offset -1 lines).
Hunk #9 succeeded at 499 (offset -1 lines).
Hunk #10 succeeded at 507 (offset -1 lines).
Hunk #11 FAILED at 539.
Hunk #12 FAILED at 549.
Hunk #13 FAILED at 568.
Hunk #14 FAILED at 593.
Hunk #15 FAILED at 604.
Hunk #16 FAILED at 624.
Hunk #17 FAILED at 635.
Hunk #18 FAILED at 659.
Hunk #19 FAILED at 670.
Hunk #20 FAILED at 693.
Hunk #21 FAILED at 704.
11 out of 21 hunks FAILED -- saving rejects to file captcha.test.rej
Due to failures show, restored original captcha module without update.php
Have I applied patch correctly ?
Comment #19
rob_roy commentedAgh ! Is this the cause of the failures ?
Should I have applied the patches in sequence ( I jumped to 05 ) ie installed 01, 02, 03, 04, 05 and run update.php after each version
Appreciate your input
Many thanks
Comment #20
soxofaan commentedAt rob_roy in #18:
thanks for taking the time to test this!
About your problem: you should always apply a patch to the latest CVS-version of the CAPTCHA module, not 6.x-2.2, that's why you got the "Hunk failed" messages.
In practice in this case, you can also use the latest nighly snapshot tar ball at http://drupal.org/node/94922
about #19: don't apply the successive version of the patches, only apply the last version in this thread (#17 at the time of this writing). In drupal development, a patch in an issue thread almost always overrules previous versions. For example, if there would be an updated patch in this thread, you should revert (undo) the previous patch before applying the new patch (the easy way here is just to overwrite everything with the original contents of the tar ball)
hope this helps
and good luck
Comment #21
rob_roy commentedThank you saxofaan for the heads up on #18 + #19 - as advised worked out
Have followed your advice and run patch on Captcha 6.x-2.x-dev on a dev site using Drupal 6.16 core using modules - Webform 6.x-2.8 with Math Captcha on bespoke forms
All previous hacks as outlined in the above posts no longer work with an error message returned about 'reuse etc'
If you need more info or further testing drop me a line - would be keen to roll out on production site
many thanks
Comment #22
soxofaan commentedOk, I guess I won't get more reviews for this patch through this thread.
The only solution is then to commit it and hope it does not break too much stuff:
http://drupal.org/cvs?commit=387414
maybe I should make a 6.x-2.3-beta release from it to get more testing.
to be ported to the Drupal 7 version too
Comment #23
soxofaan commentedcross referencing: patch at #17 contains bug #844148: Warning: Call-time pass-by-reference has been deprecated in /captcha.install on line 306, already fixed and committed for D6, but should be taken into account when porting to D7.
Comment #24
72ls.net commentedThank you for the update: CAPTCHA 6.x-2.3-rc2
It's perfect: CAPTCHA session reuse attack detected.
(^ ^)
Comment #25
solian commentedSorry incorrect Place,
moved to http://drupal.org/node/918856
Comment #26
soxofaan commentedat solian in #25: please start a new issue
Comment #27
crimsondryad commentedSoxofan,
I see the RC2 in my available updates, but the rc2 isn't showing up as "Other Releases" on Drupal.org. Not sure if this is a problem with the reskin, or with how it was posted.
Many thanks on this module...it has really helped us.
~Crim
Comment #29
crimsondryad commentedSaxofaan,
Can you push the 6.3 RC2 out as a release please? This issue has been outstanding for a long time. We will install the update and help test. If there were major issues, it seems like we would've heard by now?
Thanks!
Comment #30
soxofaan commentedYup, the 6.x-2.3 release was long overdue. Here it is:
http://drupal.org/node/967244
I was planning to tackle #825088: Exportables support for CAPTCHA points before 6.x-2.3 too, but I couldn't allocate time to work on it yet, which explains the delay for the 6.x-2.3 release. Decided it shouldn't block 6.x-2.3 release anymore.
Comment #31
crimsondryad commentedThanks bunches...we will try it out and let you know if we come across any bugs. :)
Comment #32
crimsondryad commentedOk, I installed RC2 on my staging environment this morning and got this error:
PHP Fatal error: Cannot redeclare captcha_requirements() (previously declared in /var/www/domain/webroot/sites/all/modules/captcha/captcha.module:113) in /var/www/domain/webroot/sites/all/modules/captcha/captcha.install on line 130
Comment #33
soxofaan commentedat crimsondryad in #32: are you sure you completely replaced the CAPTCHA module with a new version? I checked the tarbal for CAPTCHA 6.x-2.3 and only the file "captcha.install" contains that function
captcha_requirements(), it's not in "captcha.module" anymore (it was in previous versions, see #800846: captcha_requirements() defined in .module instead of .install).Comment #34
crimsondryad commentedNo, I'm not positive. :P It seems to be working ok other than the initial error on install though, so when we do this on prod tomorrow I'll try again completely removing it and see what happens. By "completely remove" I assume you're talking about the module files and not running an "uninstall" from the db and all. Because that would really suck considering the number of forms we have.
Sorry, that was a duh! moment...I do remember seeing the node about completely uninstalling. I just can't remember if that's what I actually did. dain bramage, FTW.
Thanks for the help, seriously. :)
Comment #35
soxofaan commentedto be taken into account for Drupal7 port of this patch:
#995748: multiple CAPTCHA protected forms on same page gives "CAPTCHA session reuse attack detected."
#844148: Warning: Call-time pass-by-reference has been deprecated in /captcha.install on line 306
Comment #36
soxofaan commentedhttp://drupal.org/cvs?commit=470426
ported and commited patch from #22, together with #995748: multiple CAPTCHA protected forms on same page gives "CAPTCHA session reuse attack detected." and #844148: Warning: Call-time pass-by-reference has been deprecated in /captcha.install on line 306
Not included however: tests related to these features/bug fixes
Comment #37
soxofaan commentedported tests too:
http://drupal.org/cvs?commit=470926
Comment #39
miroslavbanov commentedWile I was working on #2449209: Add support for cacheable captcha's (recaptcha), I noticed that you can still bypass CAPTCHA easily, but you need to pass csid and token for a solved captcha.
Comment #40
miroslavbanov commentedThe error is very simple but hard to spot.
Comment #42
wundo commentedComment #44
miroslavbanov commentedLooks like #40 needs to be fixed for Drupal-8 version as well.
Comment #45
tannguyenhn commentedYes. Same error with version 8.x-1.0-alpha0
Comment #46
aswathyajish commentedI have applied the patch captcha-session-reuse-810534-40.patch in 8.x-1.x-dev version of captcha, but it didn't work.
Also need to resolve the issue in 8.x-1.0-alpha0 version.
Comment #47
damienmckennaClosed a duplicate: #2663396: CAPTCHA session reuse attack detected (Drupal 8)
Comment #48
miroslavbanov commented@achu aji, #40 is fixing a vulnerability. Maybe you have a different problem.
Comment #49
Rajamohamed A commentedI have the same problem and I apply the patch(#2663396: CAPTCHA session reuse attack detected (Drupal 8)), Unfortunately, it not work for me.
My problem is when I added more than one file at the time appear " CAPTCHA session reuse attack detected" and I added example screen shot.
Comment #50
Rajamohamed A commentedHi,
I spend the time to this issue and found the patch(https://www.drupal.org/node/1395184) #54, it works well.
Comment #51
miroslavbanov commentedIn #39 I explain a way to reuse captcha session:
The patch is applied to 7.x, but it's not applied to 8.x. Here is 8.x version of the patch.
Comment #52
arla commentedI tried to reproduce as follows:
I get the expected failure.
Edit: Also, how come CaptchaSessionReuseAttackTestCase::testCaptchaSessionReuseAttackDetectionOnCommentPreview() does not pick up on this?
Comment #53
aswathyajish commentedI applied the patch #51 in D8 and still the 'CAPTCHA session reuse attack detected' issue exists.
Comment #54
miroslavbanov commented@achu aji
Please explain how you define the "CAPTCHA session reuse attack detected issue". #51 is about fixing a vulnerability, and the steps and expectations are listed in #52. You may be experiencing an entirely different issue.
Please list your steps. If it is a different issue, it should be opened as a separate, different issue.
Comment #55
arla commentedTo clarify #52, I could not reproduce the bug.
Comment #56
aswathyajish commentedI have an application form with file upload field and captcha. After I upload the file and enter the captcha correctly, the form does not submit. It shows an error message 'CAPTCHA session reuse attack detected'. If I again re-enter the captcha in the same page itself, the form submit successfully.
Actually, I was following the issue https://www.drupal.org/node/2663396. But it was commented and closed to follow this issue.
Comment #57
miroslavbanov commentedOK, I can verify that the vulnerability is not reproducible in D8 (it was in D7). The query doesn't run and the
tokenis not changed tonull, but the captcha reuse is still detected. The non-running query is still misleading IMO. I am hiding my patches.So this issue is about #56 I guess.
Comment #58
liam morlandPossible duplicate of #1395184: Forms with AJAX trigger "CAPTCHA session reuse attack detected." error.
Comment #59
sandeepguntaka commentedWhen there is a ajax request made before the form submit captcha token is rebuilt but not being sent to the form. so i m providing a patch to preserve the token until the form gets submitted
Comment #60
naveenvalechaComment #61
elachlan commentedComment #63
ddrozdik commentedComment #64
ahmad abbad commentedAny update ?
Comment #65
yogeshmpawarComment #66
yogeshmpawarRerolled the patch against branch 8.x-1.x
Comment #68
elachlan commentedThanks!