Problem/Motivation
I asked the security team about #3035979-131: [DISCUSSION] Should a facility be added to JSON:API which limits automatic exposure of all entities proposal 1 (
GET-only by default, but a configuration change can enable the current behavior with write access), and the nine team members who responded were all in favor of that proposal. (Didn't hear yet from @greggles or @samuel.mortenson who've given ongoing feedback here on the issue.)The proposal hardens Drupal against most more serious attacks by default, and can also be used to switch an existing site back into read-only mode in case of emergency. There's still a decent risk of information disclosure, but such vulnerabilities are generally less serious. (While SA-CORE-2019-003 was exploitable over
GETfor core REST, that is definitely the exception rather than the rule.)Marking RTBC since the JSON:API maintainers, the release managers, and at least a substantial portion of the security team can live with this compromise. (Not marking "Fixed" just yet so that others have a bit more time to respond, but note that unless we hear otherwise we'll go ahead and start implementing this proposal soon, probably first thing tomorrow, EU-time).
Note that the scope of the proposed resolution is significantly smaller than #2957061: A read only mode so that the security team could potentially recommend a course of action for sites that cannot be updated at the very moment a security fix is released, so we will probably want a new implementation issue for the "
GET-only by default" proposal. The implementation issue can discuss implementation details, specifics of the UI, how to warn users of the implications of enabling write access, etc. It should also receive usability review.
Proposed resolution
Add a read-only mode to JSON:API.
- When it's enabled, it does what it says. Everything is read-only.
- When it's off, it's just like JSON:API today.
- The default would be read-only "on".
BC break: none, we'll add an update path that automatically sets it to "off" for existing installs, resulting in existing installs undergoing zero functional change.
Remaining tasks
- ✅
Patch implementing UI + config - ✅
UX team sign-off - ✅
Patch making JSON:API respecting the config - ✅
Update path: create this configuration on existing JSON:API sites, default to "off" to not break those sites - Followups needed:
- ✅
Docs gate core blocker: Draft a handbook page (Wim has notes on the details), which we will provide to the sec team for review. - ✅
Non-blocker, major UX task: Discuss whether the site owner should see a list or table on the page of the resources that are exposed. This is the user-facing complement of what#3039715: Discuss whether we want an API routes audit status report/jsonapiprovides developers, except possibly with additional info on whether it is read-only (e.g. config entities) or writable. - ✅
Non-blocker, major or normal UX task: Discuss adding a status report entry about the setting (helpful for site audits per several people in the meeting). TBD also: whether it's a warning or info.#3039712: Discuss whether we want an entity access audit status report - ✅
Non-blocker: core critical task for 8.8.x to provide a generalized API in core that will support this for REST etc. too.#3039687: Add an API read-only mode to Drupal core.
https://www.drupal.org/docs/8/modules/jsonapi/security-considerations — issue to ensure security team reviews it: #3039959: Documentation review of the "Security Considerations" page
- ✅
- RTBC
- Commit
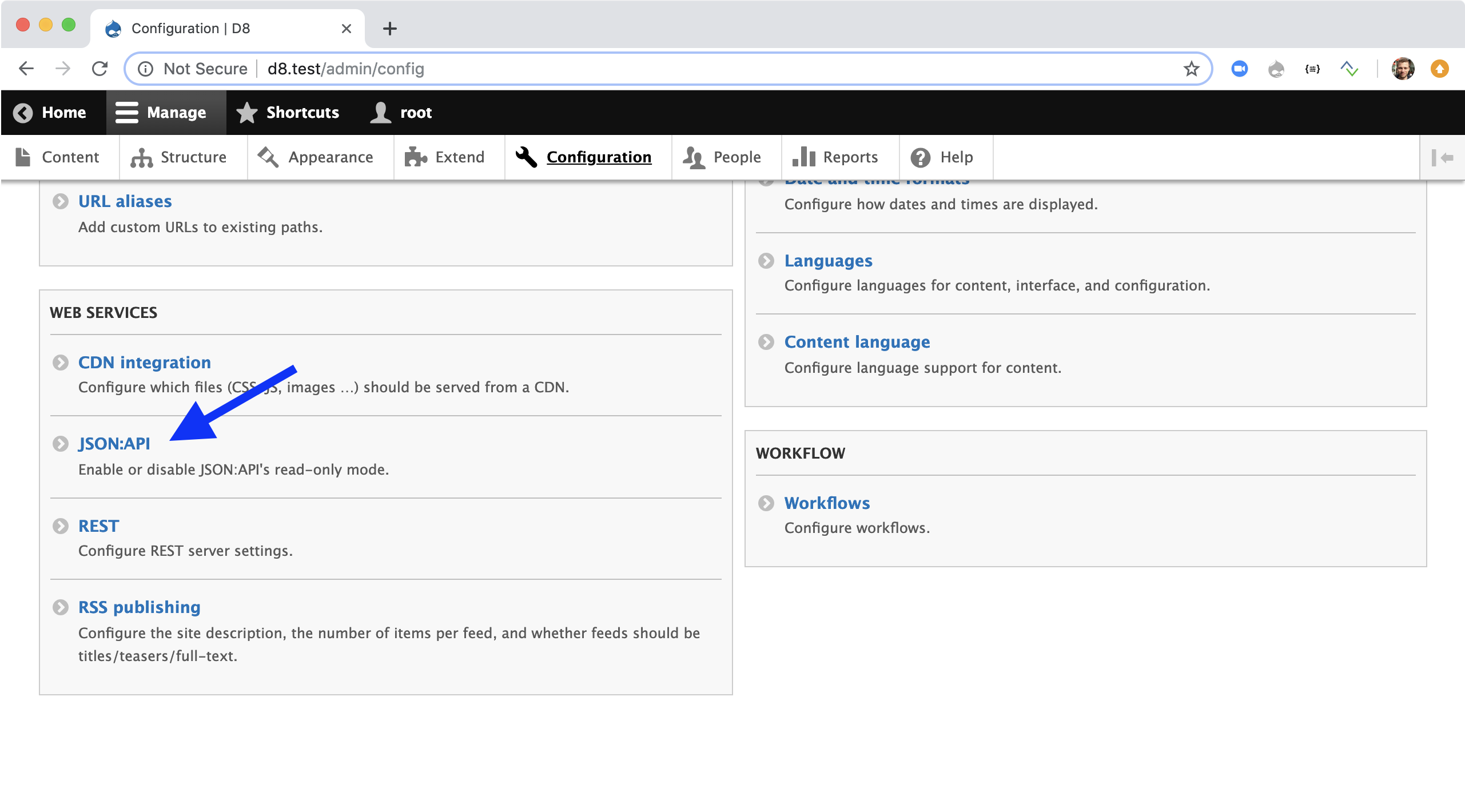
User interface changes
The first and only HTML UI is added:

it's accessible via the same UI where other web services are configured:
API changes
Data model changes
The first and only piece of configuration is added.
| Comment | File | Size | Author |
|---|---|---|---|
| #88 | 3039568-88.patch | 31.13 KB | wim leers |
| #88 | interdiff.txt | 504 bytes | wim leers |
| #48 | 3039568-47.patch | 26.73 KB | wim leers |
| #48 | interdiff.txt | 3.22 KB | wim leers |
| #48 | interdiff-41.txt | 1.19 KB | wim leers |


Comments
Comment #2
wim leersInitial patch, with UI + configuration.
Comment #3
wim leersThis makes JSON:API respect the configuration. Note that tests aren't yet updated, so this should cause a massive number of test failures, since the tests do still assume that writes are enabled by default.
Comment #5
e0ipsoOff to a great start!
This collides with JSON:API Extras. I think it's OK, we can work it out there. Can you open an issue to make sure that happens?
Let's make a not about Read-Only in the page title to show that there should not be scope creep in this config screen.
… and the configuration flag.
We probably want to include
['GET', 'HEAD', 'OPTIONS', 'TRACE']here.Comment #6
e0ipsoTwo general comments.
ResourceTypeRepository::isMutableResourceType? That'll simplify the patch quite a bit.Comment #7
effulgentsia commentedWhat about keeping the path the same, and having JSON:API Extras form_alter the form to add all of its stuff to it? In which case,
Should this description be more generic, like "Configure JSON:API"?
Alternatively, maybe we keep this description as-is, and make it JSON:API Extras's responsibility to alter it to the more generic one?
Comment #8
e0ipsoI thought about this, but I want this screen / setting to be dead simple and uncluttered.
Comment #9
wim leersThis should make most tests pass. (All if I'm lucky enough to not have missed a spot, but I'll let DrupalCI run the entire test suite instead of my machine.)
Comment #10
wim leersTalked to @xjm, she told me about the outcome of the UX team meeting. I made three changes in response to that:
I pushed back against two things:
Besides, if a contrib module truly wants to alter that form, then they can also alter this description.
Comment #11
xjmThanks @Wim Leers!
UX contributors who should be credited:
webchick, benjifisher, jhodgdon, Gábor Hojtsy, xjm, phenaproxima, ckrina, effulgentsia, wordlinemine
One thing I can't remember now whether Wim and I discussed is also potentially adding a line to the
hook_help()about it, but that's less important than the in-context docs on the form.Other things discussed with UX team that we won't implement at this point (in addition to the things Wim pushed back on above):
Comment #12
wim leers#5:
/admin/configpage. Furthermore, we can't stop contrib modules from altering stuff onto here anyway. But we can set the right example in JSON:API Extras, by having it create anExtrastab on the configuration page that this patch is adding :)#6:
ResourceTypeobject yet.#7:
See my response to #5.2.
See #10.2 (the second thing I pushed back against).
👍
#8: Then I think you'll like my response to #5.2 :)
Comment #13
xjmOh, one other nitpick that came up in the meeting is that we need the Oxford comma here:
Comment #14
xjm@e0ipso, we also discussed in the UX meeting that from a usability perspective, JSON:API extras might add its config to the same page. (It's out of scope here and not in any way something that impacts core inclusion, just was the unanimous recommendation of UX people in the meeting.)
Comment #15
xjmOops, looks like #14 was also already discussed above. Sorry, crossposts!
Comment #16
wim leersFixed CS violations, all tests should be green now. Past midnight once again. Signing off. 👋🏻
I sincerely hope there's constructive feedback awaiting me in the morning so we can get this committed in about 24 hours. 🙏
Comment #17
wim leers#13: ✅
Updated screenshot in IS, no before/after here since the difference is so tiny.
Comment #18
wim leersI mixed up screenshots.
Comment #19
wim leersComment #26
wim leers✅
Comment #27
wim leers😭One last coding standards violation: 80 cols!
Comment #28
jhodgdonMy feeling on the screenshot in #17:
- The radio options seem very clear to me.
- I am not sure the term "entities" is clear to all users. Suggest putting something in that clarifies it, like saying instead of just "entities"
entities (content items, taxonomy terms, ...)
Or something similar.
Comment #29
xjmLooks like worldlinemine also still needs to be credited as well: https://www.drupal.org/u/worldlinemine
Meanwhile, adding the followup tasks to the IS.
Comment #30
seanbI was thinking maybe we could use the word 'access' to make it more clear, and it also might not be clear what reading and writing is about for less technical users. So maybe something like:
- Allow only read access to the API.
- Allow read and write access to the API.
The part 'access to the API' might be redundant and could be fixed by adding a field label: 'Define access to the API', but just some thoughts.
I also think these need a dot at the end, like on the /admin/config/media/file-system page.
I think we discussed in the UX meeting we could probably use the Warning: prefix, similar to the permissions page. So this would then be Warning: When writing is allowed, entities can be added, changed, or removed via JSON:API. This may have security implications..
Comment #31
xjmComment #32
wim leers#29: weird, I did copy/paste their nickname too! 🤔
#28: ✅
Comment #33
wim leers#30:
🦅👁 Added the periods, great catch! ✅
I also noticed #10's refactor had a bug in the submit handler. Trivial fix.
Comment #34
dries commentedGreat progress! Thanks everyone for trying hard to get JSON:API to land.
It's a minor suggestion, but "This may have security implications." sounds a bit scary. I'd write it in a positive way: "When no write operations are required, setting JSON-API to read-only is recommended as it hardens your site's security.". The latter helps the user understand the why and feels more constructive. That extra explanation could incentivize more people to opt for read-only. Again, not a showstopper by any means, and it might have been debated in other places.
Comment #35
xjm@Dries, we also just discussed almost exactly that in the UX channel. I think Wim will have an updated patch with some changes we proposed to address making it a warning that's actionable rather than vague and therefore scary. Thank you!
Comment #36
wim leersAfter a lot of back and forth between @seanb, @xjm and I, we settled on this:
#34: Hi, Dries, nice to see you here! I believe this change also addresses your concerns!
Comment #37
seanb#36 Looks good to me! Thanks.
Comment #38
dries commentedAgree that #36 looks better!
Comment #39
andrewmacpherson commentedThis needs a
$form['read_only']['#title'], because'#type' => 'radios'is rendered as a fieldset with a legend. The patch in #36 gives us an empty legend.It could use a
configurekey in the info.yml file tooComment #40
andrewmacpherson commentedComment #41
effulgentsia commentedWhy use decoration here? Why not just add it as a separate route filter?
Based on this logic,
is_read_only_routeis incorrectly named, because it's actually telling you if it's a route that allows writes. Also, it's not handling the case where$route->getMethods()returns empty, because the meaning of that is that all methods are allowed. The jsonapi module doesn't create such routes, but we shouldn't assume that here.$all_supported_methodsis always empty. We need to add the supported methods to it.Comment #42
gabesulliceAfter catching up on this issue, this would be my ideal:
Here are my reasonings:
Let's not forget... we're adding this read-only mode because of a fear of hypothetical, as-yet-unknown bugs in preexisting entity access controls—not because we're aware of any existing or inherent flaws in JSON:API's respect for, or usage of, these public access APIs.
Regarding the follow-up:
When and where was it decided that either of these should exist at all?
I'm very -1 to this follow-up.
This is not information that the site owner should see. AFAIK, that information will be entirely unactionable and overwhelming. JSON:API's docs are already very clear about what data it exposes.
I'm also wondering about #6.2 or, alternatively, why unsafe methods are ever added in
Routes.php. Why not just prevent the routes from being created at all? (or send them to a no-op controller method likeEntityResource::getReadOnlyErrorResponse())?I think it's because the route filter allows for the generic error response, which is a DX win?
Comment #43
gabesulliceI think we also need a
configurekey in our module info file.Comment #44
e0ipsoI think the intent is that this technique is moved out of JSON:API and generalized in core. At least my reviews have had that in mind. However you are right that I have not seen a follow-up created (or mentioned) in that direction. If that is not the intent, then I agree that we should approach this differently from a technical perspective.
Can someone, please, confirm the assumption above ☝️?
Comment #45
e0ipsoWRT the error object:
It would be great if we could add a
Linkto https://www.drupal.org/docs/8/modules/jsonapi/security-considerations and have a more detailed explanation there.Comment #46
jibranI'm glad we have got here after the long discussion.
We need a hook_update_N to update the config active storage of existing sites with JSON:API installed.
Comment #47
xjmFor the followup issues, we can discuss them on the issues once filed and decide whether they're wontfix or a different fix or whatnot. :) Although I do think we want these left open to migrate into the core queue. We can move the feedback for them over once they're posted.
Comment #48
wim leers#39: Done. But we don't have UX team sign-off on that label yet :(
#41:
html_response.attachments_processor.big_pipe#42:
I do like the general direction of your description/warning, but the "You should not unnecessarily […]" statement is very confusing. And not mentioning entities at all is also making it harder to understand I think.
So I landed in the middle:
Same for the status report entry follow-up.
#43: already done for #39.
#44: That is the other key reason :) Follow-up filed: #3039687: Add an API read-only mode to Drupal core.
#45: Will look into that later today.
#46: Will look into that later today. It's already in the remaining tasks in the issue summary.
Comment #49
e0ipsoI am certain that this is the link @Wim Leers meant to link for his response to my comment on #44: #3039687: Add an API read-only mode to Drupal core
Comment #50
wim leers#47: cool, let's do that.
These are the follow-ups you added to the IS:
The remaining follow-ups have been created.
#49: yes, I just noticed & fixed that myself. 😆
Comment #51
e0ipsoEdit: cross posted.
Feedback about the documented follow-ups:
Comment #52
seanbI don’t feel I can sign off on it, but the field label and radio buttons look very good to me! I like the fact that we now explicitly mention all the operations.
I do think that
exposure to potential security vulnerabilities in the adding, changing or removing of entitieslooks a little bit scary. I would immediately think, why is there an option with potential security vulnerabilities? What are they? In the previous version of the description it stated a bit more what the risk were (adding, changing and removing content), which for some reason sound less scary to me thanpotential security vulnerabilities.On the other hand, it might be that we actually want it to look scary so people won't enable the option without knowing what they are doing. In that case, it looks good to me!
Comment #53
larowlannote to self: this is 'restrict access': TRUE
we assert before we check the JSON_API_ROUTE_FLAG_KEY? Looking at the parent implementation those without supported methods aren't removed.
does this warrant adding a utility method to the base class ... future you would approve when you have to refactor
Comment #54
e0ipsoSorry to add to the pile.
My suggestion of the UI:
to
Accept all JSON:API create, update, and delete operationsto
Accept all JSON:API read operations. Accept all create, update, and delete operations for content entities as well.Comment #55
wim leers#52: I agree it's unnecessarily scary now, which is also something @Dries made a remark about in #34. New string, which incorporates @Dries' suggestion:
#53:
$this->config('rest.settings')->set('bc_entity_resource_permissions', TRUE)->save(TRUE);in its test. It ensures that there is no risk of abstraction leading one to reason incorrectly about tests. This one particular piece of configuration is triggering a change in behavior. I don't want that to be abstracted away in my tests.RE:
restrict access: TRUE— yep, and that's also what the similar config pages use :)Comment #56
xjmThe description is getting too long for people to read. I'd really suggest going back to the description we hashed out last night because it needs to be short and declarative.
Comment #57
xjmYeah, marking NW, I don't even understand the current description when I read it. =/ It's a run-on sentence and contains so much terminology. (I'm fine with the new labels; they are clearer.) But the less text, the better.
At a minimum, let's provide screenshots of both versions of the description for UX review.
Comment #58
seanbTo be honest, I agree with @xjm that the description we had last night was a bit better. Less scary, easy to read, and understand. This does not feel like a blocking thing to me though, just a preference.
Warning: When writing is allowed, entities (content items, taxonomy terms, …) can be added, changed, or removed via JSON:API. <a href=":docs">Read more about securing your site with JSON:API.</a>Comment #59
e0ipso#56 the problem is that the shorter description did not explain all the nuances. In my opinion a security flag is not the place where you want to favor succinctness vs precision.
Comment #60
wim leersUpdate path + tests is done.
Comment #61
xjmThanks @e0ipso. I think the key thing from a usability perspective is that the handbook page is the way to properly explain the nuances, and we want people to go to the handbook page. Any UI description is too short to provide nuances and the current one is simultaneously too long and unfamiliar for site users to actually read.
Comment #62
gabesulliceThe problem with the original description is that it just described a feature of JSON:API. It was like "Warning: this module works as designed." Additionally, it's incomplete. The score security release of a few weeks ago would have been mitigated by this read-only mode even though it had nothing to do with changing entities. The attack just exploited that code path. That's why I removed the entity CRUD language.
Let's try this:
Warning: Accepting only read operations will harden the security of your site. Learn more about security hardening here.Comment #63
wim leers(Ugh I see that #55 contains a string mistake.)
#54:
#statesonly works for form items (the#type => somethinglevel), not for descriptions of form items.CRUD.#58: I think the essence of that suggestion is its brevity. It is inaccurate, because it conveys that writing entities itself is a risk, which it is not.
I combined what's in #55 and tried to respect and balance:
I ended up with:
This incorporates elements of every suggestion so far AFAICT! 🥳🤓
Comment #64
xjmMy proposal is sort of similar to the recent ones:
I pinged @jhodgdon and @clara for their UI text expertise.
Comment #65
e0ipsoI can +1 #63 (although I slightly prefer #62, but #63 is has more consensus building). The only part that is missing and we must communicate is that regardless of the option selected, no config entities can be mutated. This is very relevant and very important to this screen.
Right, but there is nothing stopping us from making that description its own
#type => 'html_tag'with that description. If that is something that you think makes sense to do.Comment #66
jhodgdonWow, lots of action during last night (in my time zone)! And in Slack, @xjm said the help text below the radios is now proposed to be
so I'm reviewing that text (not the text in #64, which I think is not as good), the rest of the screenshot in #63, and the Security page that the help text links to at https://www.drupal.org/docs/8/modules/jsonapi/security-considerations -- I have a couple of thoughts...
a) I mostly like the text on the radios. It gets across that this is only the config page for JSON:API operations, and clearly states what the two options mean.
b) On the security page at the bottom, it says that if you use read-only mode, that "completely eliminates" security problems... but is that really true? What if reading data is a possible access violation? Maybe that sentence could be changed to say that it would eliminate security problems that could affect the content of your site.
c) Regarding the help text... I am a bit uncomfortable with "the application", and also with the proposal in #64 saying "your site or contributed modules". And also that the bit explaining about entities has been omitted. Actually, entities are not being mentioned at all.
d) See also https://www.drupal.org/docs/develop/user-interface-standards/interface-text -- we're supposed to use the word "site" not "Drupal" in general, so I think "application" is also not recommended? Also it says to avoid the word "entities", which is desirable, but also in Slack yesterday we discussed that these operations only apply to entities, and people wanted to get that across.
e) Yesterday in Slack there was discussion about a module that would restrict JSON:API permissions to only certain entity types. I don't see that mentioned on the Security page or in this text.
So... Maybe this would be better:
------
Allowed operations
* Accept only JSON:API entity read operations
* Accept all JSON:API entity create, read, update, and delete operations
Warning: Use read-only mode unless the site needs write operations on entities (content items, comments, ...). Learn more about securing sites with JSON:API.
------
And then also address (b) and (e) on the Security page?
Comment #67
wim leers#65: Using
'#type' => 'html_tag'is problematic for accessibility of a form item's description.#66:
a) 👍
b) Done.
c+d) People specifically wanted to avoid mentioning "entities", since that's irrelevant for what is being communicated here.
e) will never be a thing; disabling certain entity types in JSON:API is a thing, and that's what https://www.drupal.org/project/jsonapi_extras provides, and that is mentioned in https://www.drupal.org/docs/8/modules/jsonapi/security-considerations.
Based on concerns with “application”, with “contributed modules” and @jhodgdon’s strong recommendation to use “site”:
P.S.: Let's not review https://www.drupal.org/docs/8/modules/jsonapi/security-considerations any further. Bikeshedding one thing at a time is already enough. The security team will review https://www.drupal.org/docs/8/modules/jsonapi/security-considerations. Only after that has happened, do we need to bikeshed its precise wording.
Comment #68
jhodgdon#67 discussion makes sense to me, and I think the text is clear. +1. (Have not reviewed the code, only the UI screenshots.)
Comment #69
seanb+1 from me as well!
Comment #70
xjm@Wim Leers, Maybe we can spin off a separate issue for the docs page. I did specifically ask for @jhodgdon's feedback. :) It's not a bikeshed; it's docs gate.
#67 looks good to me!
Comment #71
gabesulliceLGTM too!
Comment #72
gabesulliceFollow up tag added for the docs, per #70 and the docs needing sec. team review.
Comment #73
gabesulliceGah! I hate that tag.
Comment #74
webchickCompletely OT: Hm. Well, "followup" is not an actual word, so I can see how tag confusion would happen. :)
Reviewed the "after" screenshot from #67: https://www.drupal.org/files/issues/2019-03-13/Screenshot%202019-03-13%2...
Looks good...
1) Uses radios vs. checkboxes to make it clear what each option will do (UX pattern borrowed from private vs. public files)
2) Includes the warning about security implications, but tones it down, per @Dries and some others.
The wording of the options is quite technical. OTOH, it's also pretty technical page, and it's targeted at User 1 vs. a site builder/content author type.
One piece of feedback from the UX call that is not addressed here is the description on the overview page still is "Enable or disable JSON:API's read-only mode." which was cited as overly specific. OTOH, this seems to be a very deliberate choice, per #8, to keep this page as simple as possible.
Changing any of this is a string fix which can happen until RC so I'm not particularly fussed about it. The current version feels "shippable" to me, so +1 from me, as well. Thanks so much for the quick turnaround on this!
Comment #75
wim leers@effulgentsia pointed out this should probably be
8701, not8001for core. I'm fine with that :)Comment #76
wim leers@effulgentsia also pointed out that this should assert that the
Allowheader contains the expected value. Turns out it doesn't yet! Failing tests + fix. This wouldn't have caused significant problems and certainly no risks, but would have needed another minor bug fix in the future. Which we now can avoid!Comment #77
wim leers#70 & #72: #3039959: Documentation review of the "Security Considerations" page.
Comment #79
wim leersHAH! Pesky
Messageentity weirdness — no, just kidding, it keeps us honest — it always ensures we think about edge cases!Messageentities aren't stored so they cannot be retrieved usingGET!Also, forgot to remove the followup tag in #77.
Comment #80
wim leersDraft change record created: https://www.drupal.org/node/3039960
Comment #81
effulgentsia commentedI like this wording! Given this wording, I wonder if we want to change any of the following:
Where is this label used? Depending on the answer to that, perhaps it should be something like "Restrict JSON:API to only read operations"?
#74 mentions the UX feedback about making this less specific. However, many of the links on
admin/configare very specific. For example, "Change site name, email address, slogan, default front page, and error pages.". But given the labels of the radio buttons, perhaps this could be something like "Configure whether to accept JSON:API write operations." or "Enable or disable JSON:API write operations."?Should this be "Accepted operations"?
Should we change "enable" to "accept"?
Should this be changed to something like "JSON:API is configured to accept only read operations. Site administrators can enable write operations at %s."?
Anyway, this might have all been discussed in earlier comments (I haven't read through them all). I'm fine with punting these and/or other string changes to followups.
Comment #82
effulgentsia commentedOther than potential string changes, #79 looks great to me, so back to RTBC.
One other followup we might want:
I suspect it's possible that this is thrown in a situation where you're in read-only mode and try to PATCH a config entity. But in that situation, enabling writes won't make it work (even with that enabled, you still can't patch config entities). So in that case, we're giving a misleading error message. Perhaps we need to adjust the error message based on whether we actually filtered out the requested method?
Comment #83
effulgentsia commentedOh wait, #82 might not be an issue, because in that case, core's method filter probably throws its exception first, so perhaps we're all good there.
Comment #84
e0ipsoI will commit this in about 1h. Any other string refinement will happen in a separate issue.
Please post any additional feedback before then. Anything missed here will be fixed in another commit if necessary.
Comment #85
wim leers#81:
🤔 I think the current description is still fine. If you want to change it, I'd be okay with For now, left unchanged.
"JSON:API is configured to accept only read operations. Site administrators can configure this at %s."#82: When
POSTing a config entity for example, you'll get a 405 response even in JSON:API's current codebase, because there will only be a single route that exists for the URL you're posting to, which the routing system already generates that 405 for:No route found for "POST /jsonapi/node_type/node_type": Method Not Allowed (Allow: GET). So we're already good there 🙂 And yes, refining that can easily be a follow-up, and should be, since it's pre-existing.EDIT: while I wrote this, @effulgentsia already reached the same conclusion in #83 :D
Comment #87
wim leersSome debug code snuck in there. (Also visible in the interdiff.)
Comment #88
wim leersDiscussed #85.2 with @xjm and @effulgentsia and since this was the last thing to nitpick about, I figured we'd do it.
Comment #89
effulgentsia commentedThanks! RTBC+1.
Comment #91
wim leers🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢🚢
🥳
Comment #92
e0ipsoHa! @Wim Leers beat me to it. However, I will carry on with my plan regardless.
This issue and its predecessor were very stressful. I realize that there are a myriad of factors at play, but I think that collaborator & volunteer feelings could have been better cared for. This is often my most important value in a contrib issue queue. Hence the tradition to credit everyone that bothered to comment in an issue (yes, we've given credit to people commenting dis sux!).
Another tradition is that if an issue is particularly strenuous we'll give extra commit credit. In this case I'd like everyone to pay attention to what Wim Leers did here. He considered every nit pick, had meetings dedicated to a radio button label, posted many patches and iterations, got woken up by a bad-timing landlord after 3h of sleep… and managed to keep his spirit up and constructive while all that happened.
I know that when this is in core I won't have the chance to do this anymore with JSON:API, so here it goes…
Comment #94
dwwUgh, while I was writing this review, y'all already committed this. Ooops. :/
---
Wow, step away from the fray for a few days and lots of progress! Huzzah. :)
Mostly +1 to RTBC, with a few nits/questions/concerns:
Already mentioned, but it seems weird to use "Allowed" in this label, since the setting doesn't actually determine if the operations are allowed or not. I guess this is into "follow-up string fixes before RC" territory now, since everyone's running out of steam to make any more changes. :/
This is the only place "enable" appears on the entire form. Can we say: "Warning: Only accept all..." to match what the choices are? This seems friendly to everyone's concerns, and is a trivial fix. Perhaps still do-able before commit?
Why do we do all the work to initialize
$all_supported_methodsif we're not in read-only mode? Shouldn't the check for read-only and the early return be the first thing this method does?Can't we then avoid iterating over the entire collection twice? Can't we be building up
$all_supported_methodsin the later foreach?In short: What's the point of remembering one of the "supported" methods from a route that was filtered out already?
Not sure we need this
$is_read_only_route variableat all. Why not just:?
Thanks!
p.s. Was going to ask "Why is this specific to JSON:API at all? What about REST?" and I see that's already at #3039687: Add an API read-only mode to Drupal core. ;)
Comment #97
rpayanmMoving to Drupal core's issue queue.
I'm working on https://www.drupal.org/project/drupal/issues/3122113