Single Sign-On using Shibboleth as IdP
This document will help you in configuring SAML SSO between Shibboleth and your Drupal site. The SAML Service Provider module provides seamless integration between Drupal and Shibboleth as a SAML Identity Provider (IdP). By following these steps, your Shibboleth users will be able to log in to your Drupal site using their Shibboleth credentials.
The Drupal SAML SP 2.0 Single Sign On (SSO) module is compatible with Drupal 7, Drupal 8, Drupal 10, and Drupal 11.
Prerequisite:
- Install and activate the SAML SP 2.0 Single Sign On (SSO) - SAML Service Provider module on your Drupal site. Follow these steps to install the module.
Obtain the Drupal SAML SP Metadata:
-
After installing the module on your Drupal site, go to the Administration menu and navigate to Configuration → People → miniOrange SAML SP. (
/admin/config/people/miniorange_saml/idp_setup).
-
Copy the SP Entity ID/Issuer and SP ACS URL from the Service Provider Metadata tab and keep them handy.

Configure SAML Single Sign-On (SSO) Application in Shibboleth:
To configure Shibboleth as SAML IdP, follow the steps below:
-
In
conf/idp.properties, uncomment and setidp.encryption.optionaltotrue.
For example:idp.encryption.optional = true -
In
conf/metadata-providers.xml, use the following code to set up a Service Provider:<MetadataProvider xmlns:samlmd="urn:oasis:names:tc:SAML:2.0:metadata" id="miniOrangeInLineEntity" xsi:type="InlineMetadataProvider" sortKey="1"> <samlmd:EntityDescriptor ID="entity" entityID="<SP-EntityID / Issuer from Service Provider Metadata tab of the module>" validUntil="2020-09-06T04:13:32Z"> <samlmd:SPSSODescriptor AuthnRequestsSigned="false" WantAssertionsSigned="true" protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol"> <samlmd:NameIDFormat> urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress </samlmd:NameIDFormat> <samlmd:AssertionConsumerService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="<SP ACS URL from the Service Provider Metadata tab of the module>" index="1" /> </samlmd:SPSSODescriptor> </samlmd:EntityDescriptor> </MetadataProvider> - In
conf/saml-nameid.properties, uncomment and set the default NameID toEmailAddressas shown below:
idp.nameid.saml2.default=urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress - In
conf/saml-nameid.xml, search forshibboleth.SAML2NameIDGenerators. -
Uncomment the
shibboleth.SAML2AttributeSourcedGenerator<bean>and comment out the other<ref bean>entries:<!-- SAML 2 NameID Generation --> <util:list id="shibboleth.SAML2NameIDGenerators"> <!--<ref bean="shibboleth.SAML2TransientGenerator" /> --> <!--><ref bean="shibboleth.SAML2PersistentGenerator" /> --> <bean parent="shibboleth.SAML2AttributeSourcedGenerator" p:format="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress" p:attributeSourceIds="#{ {'email'} }" /> </util:list> -
Make sure you have defined the AttributeDefinition in
conf/attribute-resolver.xml.Note: The
AttributeDefinition idmust match the value you provided inattributeSourceIdsinconf/saml-nameid.xml.<resolver:AttributeDefinitionxsi:type="ad:Simple" id="email" sourceAttributeID="mail"> <resolver:Dependency ref="ldapConnector" /> <resolver:AttributeEncoderxsi:type="enc:SAML2String" name="email" friendlyName="email" /> </resolver:AttributeDefinition > <resolver:DataConnector id="ldapConnector" xsi:type="dc:LDAPDirectory" ldapURL="%{idp.authn.LDAP.ldapURL}" baseDN="%{idp.authn.LDAP.baseDN}" principal="%{idp.authn.LDAP.bindDN}" principalCredential="%{idp.authn.LDAP.bindDNCredential}"> <dc:FilterTemplate> <!-- Define you User Search Filter here --> <![CDATA[ (&(objectclass=*)(cn=$requestContext.principalName)) ]]> </dc:FilterTemplate> <dc:ReturnAttributes>*</dc:ReturnAttributes> </resolver:DataConnector> -
Ensure that the AttributeFilterPolicy is defined in
conf/attribute-filter.xml.<afp:AttributeFilterPolicy id="ldapAttributes"> <afp:PolicyRequirementRulexsi:type="basic:ANY"/> <afp:AttributeRuleattributeID="email"> <afp:PermitValueRulexsi:type="basic:ANY"/> </afp:AttributeRule> </afp:AttributeFilterPolicy> - Restart the Shibboleth server.
-
Once configured, you will need to use the Shibboleth Identity Provider Metadata, which follows this format:
https://example.amazonaws.com/idp/shibboleth
Configure Drupal as SAML Service Provider (SP):
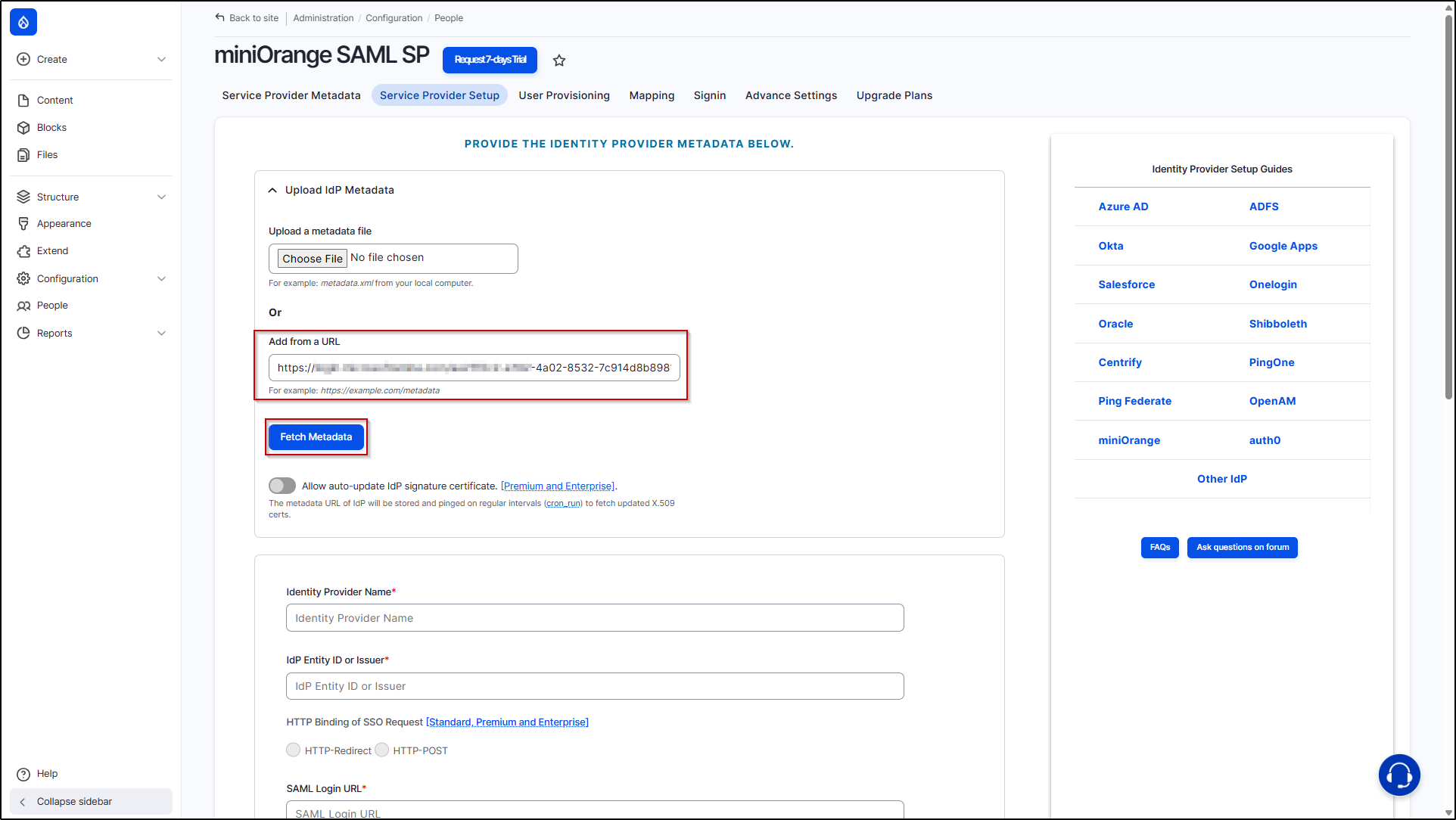
- Go to your Drupal site. Navigate to the Service Provider Setup tab of the module and click on Upload IDP Metadata.
-
Paste the previously copied "Shibboleth Metadata URL" into the Add from a URL text field. Then, click on the Fetch Metadata button.
-
After successfully saving the configurations, click on the Test link to check the SAML SSO connection between Drupal and Shibboleth.

- On a Test Configuration popup, if you don't have an active session in Shibboleth on the same browser, you will be asked to sign in to Shibboleth. After successfully logging into Shibboleth, you will be provided with a list of attributes that are received from Shibboleth.
-
Scroll down and click on the Done button.

Congratulations! You have successfully configured Shibboleth as Identity Provider and Drupal as Service Provider
If you face any issues in test configuration you can reach out to us at drupalsupport@xecurify.com with a screenshot of the test configuration window.
How does SAML SSO Login work?
- Open a new browser/private window and navigate to the Drupal site login page.
- For SP initiated SSO on your Drupal, click on the Login using Identity Provider (Shibboleth) link.
- You will be redirected to the Shibboleth login page, where the user will enter their credentials. Once successfully logged in, Shibboleth users will be able to access your Drupal site within seconds.
Help improve this page
You can:
- Log in, click Edit, and edit this page
- Log in, click Discuss, update the Page status value, and suggest an improvement
- Log in and create a Documentation issue with your suggestion
