Support for Drupal 7 is ending on 5 January 2025—it’s time to migrate to Drupal 10! Learn about the many benefits of Drupal 10 and find migration tools in our resource center.
Support for Drupal 7 is ending on 5 January 2025—it’s time to migrate to Drupal 10! Learn about the many benefits of Drupal 10 and find migration tools in our resource center.This project is not covered by Drupal’s security advisory policy.
Provides various content administration enhancements and other elements required for Open Enterprise content apps. It's purpose is to bring handy Open Enterprise UI improvements into any Drupal 7 site and to enable Open Enterprise content apps to be used on any Drupal 7 site.
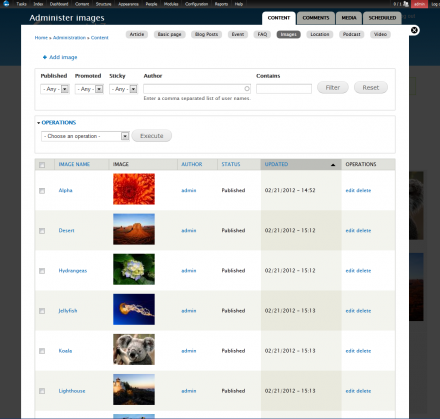
The main feature of this module is to provided some simple yet effective improvements to content admin workflows. The module adds a default admin view that is filtered by content types. This view can be overridden to show content type specific data, e.g. the date of an event. The module also adds two contextual links "+ Add [content type]" and "+ Administer [content type]" to any standard view that is filtered by content type.
Installation
There are a few ways you can quickly add this to a site:
- Traditional manual install by downloading the Enterprise Base module and dependencies from Drupal.org
- One click install via the LevelTen Apps Server. You must install the apps connector modules first.
- Start your site with the Open Enterprise Drupal distribution. The apps server connectors are included - along with a lot of other great stuff.
Issues
There is a bug in views with AJAX enabled. This will cause the admin filter and sorts not to work. A patch to fix this issue is available here:
http://drupal.org/node/1376686#comment-5481488
Sponsorship

This module is sponsored and developed by LevelTen Interactive. LevelTen is a full service interactive agency focused on building online brands by integrating digital strategy, Drupal development and internet marketing. Feel free to connect with us on Twitter and Facebook
If you would like to learn how to build smarter marketing websites with Drupal, checkout the Drupal Site Success! ebook
Project information
- Module categories: Administration Tools, Content Editing Experience, Developer Tools
254 sites report using this module
- Created by TomDude48 on , updated
This project is not covered by the security advisory policy.
Use at your own risk! It may have publicly disclosed vulnerabilities.
Releases
Development version: 7.x-1.x-dev updated 19 Feb 2012 at 00:23 UTC