 Support for Drupal 7 is ending on 5 January 2025—it’s time to migrate to Drupal 10! Learn about the many benefits of Drupal 10 and find migration tools in our resource center.
Support for Drupal 7 is ending on 5 January 2025—it’s time to migrate to Drupal 10! Learn about the many benefits of Drupal 10 and find migration tools in our resource center.Follow-up to #2342287: Allow Twig in Views token replacement
Problem/Motivation
#2342287: Allow Twig in Views token replacement introduced the ability to use twig tokens instead of custom views tokens, which means I write {{ nid }} instead of [nid]. This makes a lot of things possible.
However given that %1 and @1 still are replaced dynamically this not only means a lot of different templates are possible, but also that it might be possible to do a 'Twig-Template-Injection' attack.
Let's assume you have a view listening to giraffe/%arg
and use use %1 in one of the template.
An attacker could access a URL including {{ { '#pre_render': ['drupal_flush_all_caches']} }}.
Drupal does a simple $text = str_replace('%1', $value_from_url, $text); and boom, now you basically have a drupal_flush_all_caches()call everytime the view is rendered.
Proposed resolution
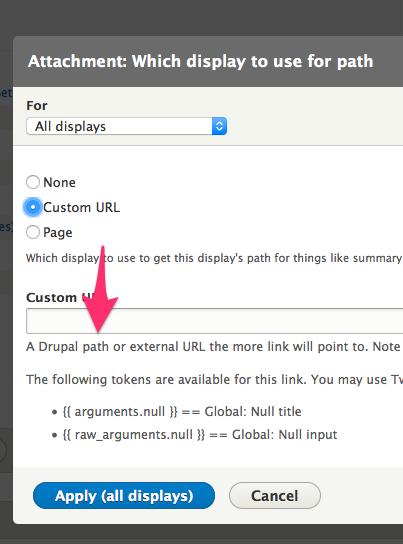
Use {{ arguments.name }} instead of @1 and {{ raw_arguments.name }} instead of %1.
Remaining tasks
- Review the patch
- RTBC the patch
- Commit the patch
- Be happy
User interface changes
- Need to use {{ arguments.name }} instead of @1 in views inline templates
- We show available replacement pattern in the common places already
API changes
- Replace @1 and %1 in views with {{ arguments.name }} and {{ raw_arguments.name }}
- Existing views will be automatically be updated.
Original report
One concern security wise for that issue:
-
+++ b/core/modules/views/src/Plugin/views/PluginBase.php @@ -320,6 +320,57 @@ public function globalTokenReplace($string = '', array $options = array()) { + // Non-Twig tokens are a straight string replacement, Twig tokens get run + // through an inline template for rendering and replacement. + $text = strtr($text, $other_tokens);Overall the straight string replacement while good for keeping BC in a way is a security nightmare.
Because if I do:
%1{%2
e.g. I might suddenly - given enough input possibilities - be able to dynamically change the twig template.
And that is "Twig-Injection-Exploit"?
I know it might not be possible, but if framework manager would allow breaking BC, the best would be to just use:
{{ tokens['%1'] }}
{{ tokens['@1'] }}instead or find some shorter variable names like:
{{ at[1] }} -- @1
{{ p[1] }} -- %1
Suggested commit credit
git commit -m 'Issue #2492839 by mikeker, joelpittet, dawehner, lauriii, Fabianx, olli: Views replacement token bc layer allows for Twig template injection via arguments'
| Comment | File | Size | Author |
|---|---|---|---|
| #154 | interdiff.txt | 2.1 KB | joelpittet |
| #154 | views_replacement_token-2492839-154.patch | 63.68 KB | joelpittet |
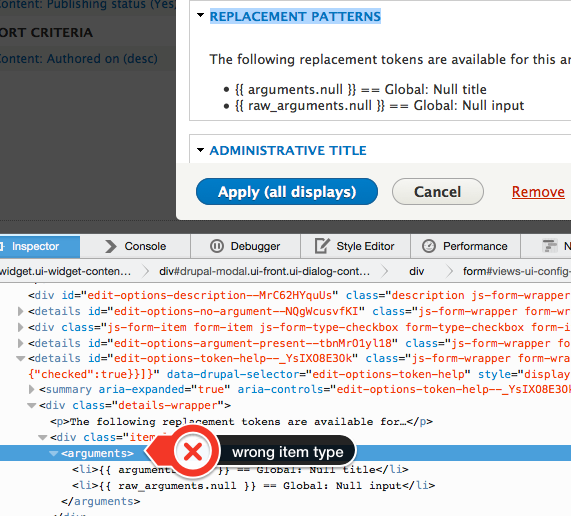
| #154 | Fullscreen_2015-09-13__2_10_PM.png | 485.71 KB | joelpittet |
| #152 | views_replacement_token-2492839-152.patch | 63.68 KB | joelpittet |
| #152 | interdiff.txt | 2.1 KB | joelpittet |












Comments
Comment #1
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedComment #2
dawehnerCan you elaborate on that sentence? I don't get that, %1 and @1 are at least not the only possible token names in views. There is stuff like
{{ body }}and what not.Comment #3
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedDawehner said that 3. is for the UI purposes, which I forgot.
1. is moot then too. I thought it checked which tokens are available in the text, but it does just remove the curly brackets that are only there for the UI.
Means we just keep point 2:
Dawehner suggested to break BC and allow e.g. {{ arguments[0] }} and {{ raw_arguments[0] }} instead of %1 and @1.
He'll comment in here shortly, too.
Comment #4
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedNeed to update the IS ...
Comment #5
jibranComment #6
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedComment #7
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedComment #8
mikeker CreditAttribution: mikeker as a volunteer commentedAwesome! The first example of a Twig Injection Exploit (now know as a TIE... maybe TIX is more cool and hip?)
Anyhow, we should probably hold off on this until #2466931: Valid Twig syntax is incorrectly escaped in Views rewrites is sorted. Also, the CR from #2342287: Allow Twig in Views token replacement will need to updated.
Comment #9
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedI think this issue is orthogonal to the other one, tagging also revisit before release candidate, because while not critical it makes me uncomfortable overall still ...
Comment #10
mikeker CreditAttribution: mikeker as a volunteer commentedComment #11
mikeker CreditAttribution: mikeker as a volunteer commented#3:
Just to clarify,
%1is the raw argument and!1is the raw argument that's been run throughstrip_tags(Html::decodeEntities($arg)). There is no@1token. At least that's how I read it (ViewExecutable.php@1036). @dawehner, can you verify?So the proposal is to replace
!nand%nwith Twig arrays {{ raw_arguments }} and {{ arguments }}, respectively. Previously, the argument tokens were 1-based while arrays are zero-based, so%1would be replaced by{{ argument[0] }}. I'm fine with that, but wanted to make sure no one else objects...Another option would be to use the argument ID as the key to the Twig arrays. Eg:
{{ arguments['uid'] }}. This avoids the zero- vs. one-based indexing but we would need to expose the argument IDs somewhere -- probably similar to the "Replacement patterns" details element when rewriting fields.Comment #12
mikeker CreditAttribution: mikeker as a volunteer commentedI've found something else to confuse things: core/modules/views/src/Plugin/views/field/FieldPluginBase.php@871 says:
which implies that the % argument is not a raw value so much as the argument title. But that doesn't seem to be how it operates. If I rewrite a field as "%1 and !1" it results in "foo and foo" not "uid and foo" or "Author ID and foo".
Comment #13
star-szrJust a small note,
{{ arguments['uid'] }}can be also written as{{ arguments.uid }}in Twig.Comment #14
mariagwyn CreditAttribution: mariagwyn commentedEDIT: posted here https://www.drupal.org/node/2543796. Leaving this for reference.
=========================
This may not be the correct place to post this issue, so I can repost elsewhere.
Using D8-beta13 I attempted to use a token in a view to rewrite the CSS output:
1. Under Style Settings in the field configuration, select 'create a css class'
2. Insert:
icomoon-{{ field_icomoon }} headingwhere '{{ field_icomoon }}' is the replacement token grabbed from the 'rewrite results' section.3. Save
When a page with the block is loaded, the "website encountered an unexpected error". Console output shows:
[Thu Jul 30 16:52:36.495200 2015] [fcgid:warn] [pid 17226:tid 3015823360] [client 127.0.0.1:52474] mod_fcgid: stderr: Uncaught PHP Exception Twig_Error_Syntax: "Unexpected token "end of template" of value "" in "{# inline_template_start #}icomoon-{{" at line 1" at /core/vendor/twig/twig/lib/Twig/ExpressionParser.php line 190, referer: http://local.site/admin/structure/views/view/servicesNote:
1. same replacement token works without error in the "Rewrite Results" section.
2. CSS replacement works if it does not contain the token.
Comment #15
mikeker CreditAttribution: mikeker as a volunteer commented@mariagwyn: #14 would be better off in a separate issue. I updated the title of this issue to be more specific.
Comment #16
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commented#15: Will you be able to work on this in the near future?
We are getting ever closer to release candidate and I fear I will need to make that issue critical then (at RC 1 checklist time) (for security reasons), which would probably mean that the original issue is rolled back for simplicity.
I still think this is totally doable with less effort, so not doing so, yet.
Comment #17
mikeker CreditAttribution: mikeker as a volunteer commented@Fabianx: I can take a stab at it, but I'm on vacation right now and my dev time is limited to the hour-or-so I get while my wife does yoga! :P
I would really, really hate to see #2342287: Allow Twig in Views token replacement rolled back because of this...
Comment #18
mikeker CreditAttribution: mikeker as a volunteer commentedWork in progress...
Comment #19
mikeker CreditAttribution: mikeker as a volunteer commentedIs there any way to hand Twig an array in Twig format (eg: foo.bar.baz) instead of as proper PHP array? I'm worried that changing Views' tokens from a string to an array will be too disruptive to get in this late in the game...
Or we can keep this kludge and add a @todo and a followup issue.
Comment #21
mikeker CreditAttribution: mikeker as a volunteer commentedThis should fix a few tests...
Comment #23
mikeker CreditAttribution: mikeker as a volunteer commentedUpdates some docs and description fields and fixes some tests.
Comment #24
mikeker CreditAttribution: mikeker as a volunteer commentedIn
core/modules/views/src/Tests/Handler/AreaEntityTest.php:130the test uses Views' preview function and sets the result as the raw content:Can anyone explain why we use this method rather than rendering the View for real? At first glance, there may be a bug in Views' preview that prevents the token from rendering correctly, but it works as expected when the view is rendered normally.
Comment #26
mikeker CreditAttribution: mikeker as a volunteer commentedTo answer my own question, it's because you can pass arguments to preview(), but not render() as those are pulled from the request object.
This patch should fix up more tests and remove more instances of ! and % tokens.
Comment #28
mikeker CreditAttribution: mikeker as a volunteer commentedThis should take care of a couple of the failures. I would appreciated any help on the remaining exceptions as I won't have much time in the next few days to work on this.
Basically, it throws the exception in Views' preview mode or when running tests, but doesn't when rendering the view regularly.
Comment #30
joelpittetTagging for twig visibility
Comment #31
jonathanshawRC1 is imminent, this issue is now at top of the "issues to revisit before RC" list.
@Fabianx warns in #16 that #2342287: Allow Twig in Views token replacement is likely to be rolled back if this issue is not fixed.
Comment #32
mikeker CreditAttribution: mikeker as a volunteer commentedRerolled.
PluginBase.phpwas a fair bit of change so I included an interdiff. Waiting to see what the testbot says before moving on.@jonathanjfshaw: Remaining items on this issue is pretty clearly laid out in #28 and #19. (The code in #19 is made a bit more wonky by the latest reroll).
Comment #33
mikeker CreditAttribution: mikeker as a volunteer commentedOops. Fix coming soon.
Comment #35
olli CreditAttribution: olli commentedThat "-" in test-token is not valid?
Some extra space.
That else{} looks unreachable now and can be removed? Just to avoid reverting the other issue, would it help to run that strtr() after rendering the inline template?
$substitutionsis missing "{{" and "}}".This looks like a global token. Do we need to replace those too?
#28: Filed #2564475: LogicException: Render context is empty in views ui preview.
Comment #36
catchComment #37
mikeker CreditAttribution: mikeker as a volunteer commented#33: Fixed.
#35: Thanks for the review @olli!
Nope. Fixed.tests
Fixed.
I think that is left over from an earlier approach to this issue and can be removed. At the moment it's not doing anything since
viewsTokenReplacedoesn't take a reference to a string. I've removed it in this patch.I don't understand how that would help... Can you clarify? Thanks.
Fixed. I keep on missing those...
Not sure. That was needed to make the tests work, but I need to look at it again to see what's happening...
Comment #39
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedI was able to easily reproduce this with a view by adding a Node: ID argument and using exclude rather than include, but then I was not able to actually break out of twig land to do something ...
So putting in argument: {{ nid }} or title worked well, but difficult to do something else as there is no object available in that scope.
I have not yet tested what I can do when I create a render element on the fly however.
Comment #40
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedOkay, I found a way not to delete an entity (#lazy builder and #pre_render are amazingly well protected against anything not using scalar values), but to at least DDOS the site:
Given a view that has a Node: ID argument that is set to exclude rather than filter and a rewritten views field like title that uses that argument either %1 or !1 you can use:
views/[name]/{{ { '#pre_render': ['drupal_flush_all_caches']} }}OR
views/[name]/{{ { '#lazy_builder': ['drupal_flush_all_caches', []]} }}OR
views/[name]/{{ { '#post_render': ['drupal_flush_all_caches']} }}Given that and because catch asked me to make this critical before todays Critical Triage Call, I am marking this critical.
Comment #41
dawehnerGiven that this is a security problem, we should add some test to ensure it actually works and does not allow you to execute code.
On top of that we need an update path + update path testing, happy to do that.
Comment #42
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedGiven this now has an 'exploit' of sorts, this is now a security issue (D7 not affected obviously) and hence adding 'security' tag.
Comment #43
fgmSecurity-wise, is it correct to say the impact is mitigated by the fact that this is only exposed to authenticated users with the "Administer views" permission, which is marked as having administrative impact ?
Comment #44
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commented#43: No, any view that exposes an argument and where the trusted user has added a Node ID argument for exclusion but used that within the view somewhere in a rewrite:
e.g.
mycontent-page/1
shows:
Here is all content except for Node '%1' and it excludes the Node ID that was added in the URL.
That scenario is artificially constructed, but I know that I used 'exclude' in real views before in D7 and I also know I used to show arguments in rewrites as well (or used them in decision making), so it is not totally artificial ...
The problem is that the way the strtr() works is inviting the user that puts the argument into the url to change the twig template before it is displayed.
e,g,
Consider the following way:
- Using an argument for exclude with the following template (which would indeed be a misuse of arguments, but ...):
If a user now enters a 'template' into the URL as argument %1 as suggested they can change this template into:
Basically where the %1 was the user of the site has full control of the twig template. I had hoped it was not possible to exploit this (major bug), but as I was able to, so it is now critical.
Comment #45
catchChanging the title to reflect the bug a bit better.
Comment #46
dawehnerAlright, this is not 100% the case fabian had, but still, it shows that things are problematic.
Comment #48
dawehnerStarted with some rudimentary update path. I'm pretty convinced that these aren't all the possible configurations yet.
Regarding arguments.1 vs. arguments[1] vs. arguments.machine_name, I would think at that point we should go with the number, just because people are used to that.
Comment #50
pwolanin CreditAttribution: pwolanin as a volunteer and at Acquia commentedCan you clarify in the issue summary why having those longer variable names is more secure?
Comment #51
dawehnerSure, but its written down pretty good in #2492839-40: Views replacement token bc layer allows for Twig template injection via arguments
Comment #52
mikeker CreditAttribution: mikeker as a volunteer commentedOne advantage of going with the number is it makes the upgrade path code a lot easier! But I've always hated having the token names tied to the order of the contextual filters not to mention the ever-present confusion over one- vs. zero-indexing them...
(Also, just for clarification, arguments.1 and arguments[1] are identical to Twig in this context.)
Comment #53
xjmThis is now critical so "revisit before release candidate" is now redundant. :)
Comment #54
xjmAh, as is "rc target".
Comment #55
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commented#50:
The criticalness is not the naming, but the fact that user input is executed as a twig template.
So even if we had:
- %really_long_name it would still be problematic.
And there is no technical difference - except for the user / UX - between {{ arguments.1 }} and {{ arguments.some_nice_name }}.
Both would solve the issue as then whatever you put in as argument would in Twig land then just be a string, which you then can print, but which is auto-escaped, etc.
So this would all be fine.
Comment #56
lauriiiI was playing around with this and fixed some of the tests on the way.
Comment #61
dawehnerExported a test view which should have everything you can imagine for the update path.
Comment #66
joelpittetDiving in here and reviewing the code straight away:
Don't we still need to return the text if there are no twig tokens? I don't see any early exiting added.
FYI I'm also a proponent to using named arguments if possible here. The order of the arguments make reading views export quite tricky, this would be a nice DX improvement if we can pull it off. +1.
Note to self: find out if the t() can be removed from the keys here for our other issue returning TranslationWrappers from t()
Do we need a token list here or just examples like before?
Needs a docblock and maybe better values to test? Meh
This looks backwards. % is arguments and 6 and test1 should be 5.
Surprised this works.
Though long this may be better multi line.
nit: remove extra line break.
Comment #67
dawehnerWorking on this for a while.
Thank you for the review @joelpittet
Comment #68
dawehnerFixed parts of the review, expanded the test coverage, sighing off for tonight
Comment #70
joelpittetLess of a review more of a praise:)
This is a good change as it's unlikely a token will attach assets:)
Whoa cool way to test upgrade path, didn't know that was possible.
Comment #71
mikeker CreditAttribution: mikeker as a volunteer commentedWorking on fixing the tests...
Comment #72
mikeker CreditAttribution: mikeker as a volunteer commentedQuick summary of changes:
Comment #76
joelpittetGoing to try to tackle the remaining failures, nice cleanup and fixes @mikeker and @dawehner!
Comment #77
joelpittetSince we are using renderPlain the mock parameter count needed to change and method it expected.
Comment #78
joelpittetThis is my biggest concern: This change looks wrong. I'm quite sure it needs to return
$textstill. Can't someone explain this?re #72Thanks for adding the comma @mikeker. Was the 'text' token name needed? It wasn't mentioned in your summary of changes.
Comment #79
mikeker CreditAttribution: mikeker as a volunteer commented#78:
I think that's a oddity in how the diff looks... That line (
core/modules/views/src/Plugin/views/PluginBase.php:406) comes right after the inline template is built and passed the Twig tokens. Returning $text would negate the purpose of the function.I'm planning to be on the Twig conf call tomorrow morning -- we can chat about this before/after to make sure we're talking about the same thing...
Sorry, missed that one. Yes, it's needed for
$data['display']['default']['display_options']['fields']['title']['alter']['text']incore/modules/views/src/Tests/Update/ArgumentPlaceholderUpdatePathTest.php:37. Crazy array! :)@joelpittet, Thanks for getting this patch green!
Comment #80
dawehnerNice! Thank you
Expanded the test coverage, show the tokens on arguments.
Comment #81
dawehnerWrote a CR, updated the issue summary with the proposed solution.
Comment #82
lauriiiIf there is no tokens to be replaced we should still return the $text because it might be just static text.
This is going to have problems after #2557113: Make t() return a TranslationWrapper object to remove reliance on a static, unpredictable safe list , see also #2561259: Cast (optgroup) array keys that may hold translated strings to string
These could definitely use a message
I think the message is not correct anymore
Comment #83
dawehnerThank you for your review @lauriii!
I do agree, its preventing a potential future bug indeed. I'm pretty sure we have an if everywhere before calling this function, but better be safe than sorry.
Let's cast it to a string already. In general though this is existing code and not something this patch really introduces.
Good point
Ha you are right!
Comment #85
dawehnerSeemed to be a random test failure.
Comment #86
dawehnerCleaned up the remaining tasks
Comment #88
mikeker CreditAttribution: mikeker as a volunteer commentedThanks @dawehner!
And apologies to @joelpittet who talked about the need for returning $text but I was misunderstanding what he meant. I'm not convinced you can reach that else clause but, as @dawehner says, better safe than sorry. Along those lines, we should
Xss::filterAdminthe value to be consistent with other return values from this function.Comment #89
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commentedI would like to understand why this change is needed. And what fails if we don't do that.
Overall the tokens should be just strings, but just saying (and not sure that is good or bad), this limits e.g. the capability to attach a library (don't do that!) or render something more complex in the future.
This change is wrong now that we use the machine names.
Nice!
I believe this is what fails if that other thing is ->render() instead of renderPlain().
Should be wrapped in executeInRenderContext(new RenderContext(), function() {
});
then it works.
Besides that, looks great!
Comment #90
mikeker CreditAttribution: mikeker as a volunteer commentedThanks, @Fabianx, for the review! From #89:
Views rendered in preview mode were throwing exceptions (see #2564475: LogicException: Render context is empty in views ui preview). Some tests use preview to render views as it's easier to pass arguments (see test results in #28).
Agreed, it limits our ability to attach assets in the future, but I think that's ok. Maybe?
2: Fixed. Ideally we would link to a d.o docs page that better describes the values in
argumentsandraw_arguments.4: I tried that at one point but wasn't able to get it working (see this gist). But I don't really understand render contexts so I may have been doing it completely wrong!
Comment #91
dawehnerWhat about adding a todo to investigate whether we want to create a render context in the future? When I tried to fix the failure I was just too lazy to create the additional code to create a render context :p, but at least for tokens its really not needed.
mikeker++
Comment #92
Fabianx CreditAttribution: Fabianx as a volunteer and at Tag1 Consulting commented#90: Given this is critical and there are no assets currently, this is fine , if:
- we have a major follow-up bug / limitation issue
- and add a @todo pointing to that new issue
Thanks!
Comment #93
mikeker CreditAttribution: mikeker as a volunteer commentedAdded followup and @todo: #2566621: [Follow-up] PluginBase::viewsTokenReplace uses renderPlain which may limit the use of attached assets.
Comment #94
dawehnerThank you @Fabianx and @mikeker
I agree we should maybe rethink whether we should have those execution wrappers at a higher level to be honest.
Comment #95
lauriiiTested this manually by using the arguments in view title and field override. I was unable to execute Twig and tokens where replaced as supposed to. Also the patch looks good for me.
Comment #96
joelpittetI think it should be fine with
Renderer::renderPlain()because we really shouldn't be doing asset additions in tokens. And if that is needed, it can be a feature request or follow-up as we have it.Fixed a couple nitpicks.
Trying to figure out how to get the tokens to work with global null
views.nullfor the remaining!1token forAreaEntityUITest.Comment #97
joelpittetWorking on the latter part of #96 unless I'm wrong, feel free to stop me:)
Comment #98
joelpittetOk that was easier than I thought:)
Comment #99
mikeker CreditAttribution: mikeker as a volunteer commentedBoth the changes in #96 and #98 look good to me. Thanks for correcting my grammar! :)
Comment #100
joelpittetThis patch fixes this little UI thing(kinda makes it worse looking but correct markup and that's CSS for item list in views fault):
Comment #101
joelpittetMissed a couple more of those and tried to make the #description that was being built up on there be consistent with the exact same build up.
Found by searching for this:
foreach ($this->view->display_handler->getHandlers('argument') as $arg => $handler) {Here's a screenshot after to show I didn't break things by moving it to a render array instead of drupal_render().
Comment #102
joelpittetOk feel free to RTBC away @lauriii;)
Comment #105
mikeker CreditAttribution: mikeker as a volunteer commentedI feel we need to lock down this issue. We're starting to add nice-to-haves and I'm afraid that will destabilize the fix we have consensus on.
@joelpittet is absolutely correct that
'#list_type' => $typeis wrong and results in bogus HTML. But it turns out there were tests that relied on that bogus HTML (who knew...).Let's not let perfect get in the way of pretty-good!
Along those lines, #66
should be opened as a followup.
Comment #106
mikeker CreditAttribution: mikeker as a volunteer commentedComment #107
lauriiiThanks joelpittet and mikeker for the additional fixes!
Comment #108
lauriiiReposting latest patch because it is not listed in the files list and seems like PIFR cannot find it.
Comment #109
joelpittetOh and of course the tests are checking for
<fields>in xpath. Here's a fix for that.Comment #110
joelpittetDang cross posted with both of you! I should have just went to bed:P
Comment #111
alexpotttitle: '%1'- it was added relatively recently - #1739846: Tests taxonomy argument validator pluginMissing documentation for $argument_map
Missing documentation for $displays
Unnecessary new line
Nothing wrong with this patch because this is fixed elsewhere (by the checkPlain() work) but this test is nicely absurd. It is testing that we have a double escaping bug :)
Comment #112
joelpittetLOL nice catch on the double escaping test, I thought I read that but I guess not thorough enough.
Comment #113
joelpittetFixed the items in #111. And added an extra double escape test to ensure we don't have any more. The double escaping was on the concatenation of a previously escaped admin_label passed in an @ then concatenated to ' == '
Comment #114
joelpittetSelf-reivew.
Comment #115
alexpottI'm really sorry - I was just pointing out the double escape test cause it is funny. Fixing this is not in scope for this issue. I should have been clearer.
Let's revert this.
Comment #116
dawehnerThank you alex!
Here are some additional nitpicks, we can fix them later if we want though
Could we use some of assertEscaped/assertNotEscaped for those?
I'm curious whether given that this method could be called quite often as well, we could use strpbrk
Do you mind adding a follow up maybe even in twig itself to have a constant to validate those properly
Can we add some explicit test coverage for that? I guess its not possible because you never actually reach this point?
Nitpick: new line needed
Comment #117
alexpottThe issue that covers the double escaping bug is #2564283: Remove use of SafeMarkup::checkPlain() from adminSummary() and adminLabel() in views plugins
Comment #118
joelpittetI miss-interpreted the review in #111.5 That crappy test was already there we just swapped out the guts. I'm reverting that.
He was referring to #2564283: Remove use of SafeMarkup::checkPlain() from adminSummary() and adminLabel() in views plugins which deals with that test and more.
Comment #119
dawehner@joelpittet
Feel free to fix my other points.
Comment #120
joelpittet@dawehner re #116
0) That will move to the other issue.
Comment #121
dawehnerWe used it in #2492967: SQL layer: $match_operator is vulnerable to injection attack as well
Ah I see its used in #114, I think I reviewed something before that
Comment #122
mikeker CreditAttribution: mikeker as a volunteer commentedre: #116
1: Learn something new every day in this issue queue! :)
I would like to profile strpbrk vs. strpos vs. strcspn. Should be a follow-up, IMO.
2: Added #2567269: Create a Twig regex constant or function that validates a Twig variable.
3: As you say, I think it will be hard to add a test for that as I can't think of a way to reach that else-block. It was added as a better-safe-than-sorry.
4: Dude, @joelpittet is on it! :)
Comment #123
mikeker CreditAttribution: mikeker as a volunteer commentedAlso, not sure what the protocol is for this, but I believe @Fabianx and @olli should be added to the Dreditor-supplied commit message for their code reviews and that @Fabianx found the vulnerability that made this a critical. Thanks for considering it.
Comment #124
joelpittetI'm not totally sure the protocol myself but I believe you just add it to the issue summary.
git commit -m 'Issue #2492839 by mikeker, joelpittet, dawehner, lauriii, Fabianx, olli: Views replacement token bc layer allows for Twig template injection via arguments'Comment #125
davidhernandezIdeally, we'd want anyone who should get credit to comment on the issue so they appear in the credit area at the bottom of the page. That info is stored in drupal.org.
Comment #126
olli CreditAttribution: olli commentedDoes this drop support for global tokens in entity area plugin, are they still listed in the ui as available global tokens?
:is not allowed?Did anyone check other places that use global tokens for possible injection?
arguments.name->arguments.nullnull,ull->'null'Is this same as
?
base_field: id?
'entity' is missing
$changed = TRUE;missingnot implemented.
Comment #127
dawehnerThank you @olli, really good review!
We thought about that previously, this is the reason why it isn't:
So the global tokens come afterwards.
It indeed seems to be the case that this field is not used at all, well I copied this test view from somewhere.
Really good catch!
As I realized, this $changed = TRUE just makes sense when
_views_update_8002_token_update()is actually called.Also very good point!
It indeed is
Comment #129
olli CreditAttribution: olli commentedOk thanks.
Sorry I meant that isn't it 'null' in quotes, a string.
Comment #131
dawehnerWhy would yaml care about that? Strings in yml don't need quoets. Maybe I misunderstand you ...
Comment #132
olli CreditAttribution: olli commentedI believe it cares if you need a string "null", "true" or "false".
Comment #133
dawehnerOh, you are too clever. Feel free to just patch it, I'm afk
Comment #134
plachAnd here it is, please don't credit me.
Comment #137
plachThe failure seems unrelated
Comment #138
plachBack to RTBC
Comment #139
dawehnerIndeed this is how an export looks like in real life:
So we need some two more adaptions.
Comment #142
joelpittetI'm working on this fail, but if you know the solution by just looking at it I'd not be mad if you just post a patch;)
Comment #143
joelpittet@dawehner gave me a hint, the key itself doesn't need to have strings. I ran through tests to ensure that was correct with a breakpoint after the change.
Comment #144
joelpittetNope that should have worked actually. digging deeper into the test to see what's up. It looks like the placeholders not there but there is an escaped
pre_renderstill in there. So technically it won't get executed(good), but will try to render that to the screen I believe.Comment #145
joelpittetOk resolved this. YAML treats null: keys as NULL so that gives you {{ arguments. }} which is wrong. @dawehner's export is correct in quoting that value.
The problem was that the arguments passed in to test if #pre_render doesn't execute were being escaped and that would be the output. So I think the correct solution is to change the test to what we expect the output to be based on the input.
Comment #146
mikeker CreditAttribution: mikeker as a volunteer commentedCould we use a nid argument and void the whole NULL vs. "null" bit?
Comment #147
dawehnerWe could for sure, but then we would have to set exclude: true in the argument configuration.
Mh Interesting, but its kinda what we want, indeed
Comment #148
dawehnerI think we could expand the test coverage in a follow up, don't we?
For now let's use the NULL argument, which works fine, when we use the quotes, as the export does.
Comment #150
joelpittetRe-rolling.
Comment #151
joelpittetJust a conflict with someone who did some of the casting to string stuff that we didn't want in this patch was committed already.
Setting back to RTBC.
Comment #152
joelpittetWhoops my merge missed the
$arg =>somehow.Comment #154
joelpittetProbably not helpful but this is the re-roll interdiff to show what changed since.
Ok enough mistakes to let someone else RTBC:P
Comment #158
dawehnerYou know, things happen, let's see whether its green again ...
Comment #159
dawehnerIts green, the merge was successful.
Comment #160
alexpottCommitted 9aec827 and pushed to 8.0.x. Thanks!
Comment #162
neclimdulquick follow up. #2568415-2: 2492839 added invalid yaml
Comment #164
amateescu CreditAttribution: amateescu for Pfizer, Inc. commentedThe change record for this issue (https://www.drupal.org/node/2566251) was still a draft, I published it now :)
Comment #165
joelpittetThank you @amateescu